600K WordPress sites impacted by critical plugin RCE vulnerability

Reading Time: 1 Minute
Essential Addons for Elementor, a popular WordPress plugin used in over a million sites, has been found to have a critical remote code execution (RCE) vulnerability in version 5.0.4 and older.
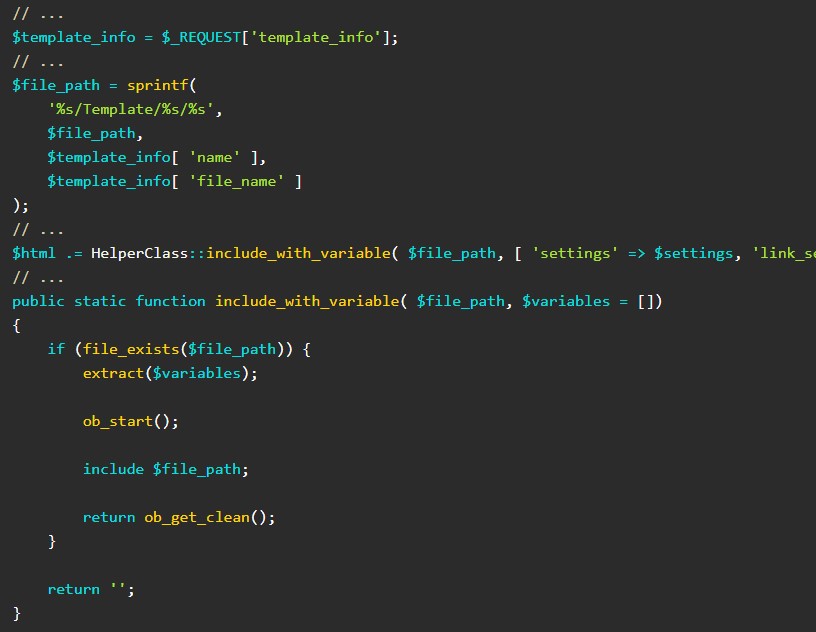
The flaw allows an unauthenticated user to perform a local file inclusion attack, such as a PHP file, to execute code on the site.
“The local file inclusion vulnerability exists due to the way user input data is used inside of PHP’s include function that are part of the ajax_load_more and ajax_eael_product_gallery functions.” explains PatchStack researchers who discovered the vulnerability.
The only prerequisite for the attack is for the site to have the “dynamic gallery” and “product gallery” widgets enabled so that a none token check is present.
Source: Patchstack
Two failed patching attempts
Researcher Wai Yan Muo Thet discovered the vulnerability on January 25, 2022, and the plugin developer already knew about its existence at that time.
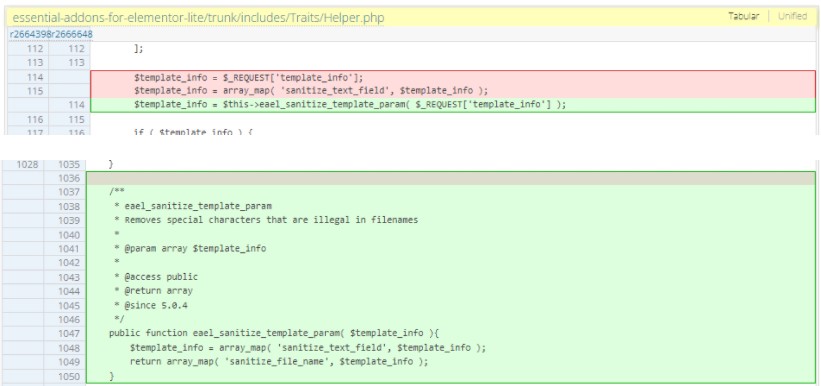
In fact, the author had released version 5.0.3 to address this issue by applying a “sanitize_text_field” function on the user input data. However, this sanitization doesn’t prevent the inclusion of local payloads.
The second attempt was version 5.0.4, which added the “sanitize_file_name” function and attempted to remove special characters, dots, slashes, and anything that could be used for overriding the text sanitization step.
Source: Patchstack
This was the version that Patchstack tested and found vulnerable, so they informed the developer that the fix hadn’t mitigated the issue sufficiently.
Eventually, the author released version 5.0.5 that implemented PHP’s “realpath” function, preventing malicious pathname resolutions.
Update and mitigate
This version was released last week, on January 28, 2022, and at this time has only been installed approximately 380,000 times according to WordPress’ download statistics.
With the plugin installed in over 1 million WordPress sites, that means there are over 600K sites that have not applied the security update yet.
If you are among the many that use Essential Addons for Elementor, you can get the latest version from here or apply the update directly from the WP dashboard.
See Also: Recon Tool: WitnessMe
To prevent actors from leveraging local file inclusion flaws even when they can’t be directly mitigated, follow these steps:
- Save your file paths in a secure database and give an ID for every single one.
- Use verified and secured allowlist files and ignore everything else.
- Don’t include files on a web server that can be compromised, but use a database instead.
- Make the server send download headers automatically instead of executing files in a specified directory.
See Also: How ILOVEYOU worm became the first global computer virus pandemic
Source: bleepingcomputer.com
(Click Link)












