A new Browser-in-the-Browser attack led hackers steal Steam accounts

Reading Time: 3 Minutes
Hackers are launching new attacks to steal Steam credentials using a Browser-in-the-Browser phishing technique that is rising in popularity among threat actors.
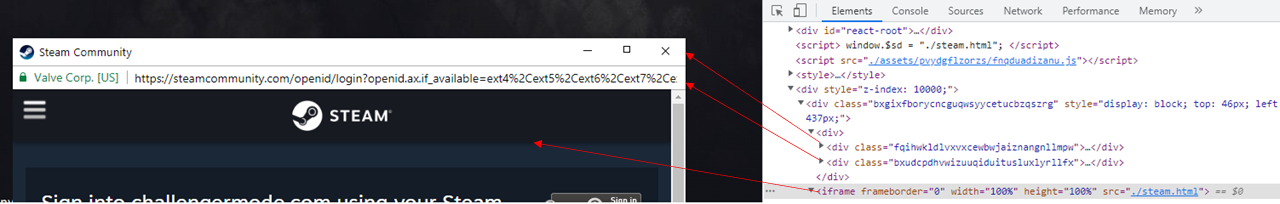
The Browser-in-the-Browser technique is a trending attack method involving the creation of fake browser windows within the active window, making it appear as a sign-in pop-up page for a targeted login service.
In March 2022, BleepingComputer was the first to report on the capabilities of this new phishing kit created by security researcher mr.d0x. Using this phishing kit, threat actors create fake login forms for Steam, Microsoft, Google, and any other service.
Today, Group-IB published a new report on the topic, illustrating how a new campaign using the ‘Browser-in-the-Browser’ method targets Steam users, going after accounts for professional gamers.
These phishing attacks aim to sell access to those accounts, with some prominent Steam accounts valued between $100,000 and $300,000.
See Also: So you want to be a hacker?
Complete Offensive Security and Ethical Hacking Course
Baiting with tournament play
Group-IB reports that the phishing kit used in the observed Steam campaign isn’t widely available in hacking forums or dark web markets. Instead, it is used privately by hackers that come together on Discord or Telegram channels to coordinate their attacks.
Prospective victims are targeted with direct messages on Steam, inviting them to join a team for LoL, CS, Dota 2, or PUBG tournaments.
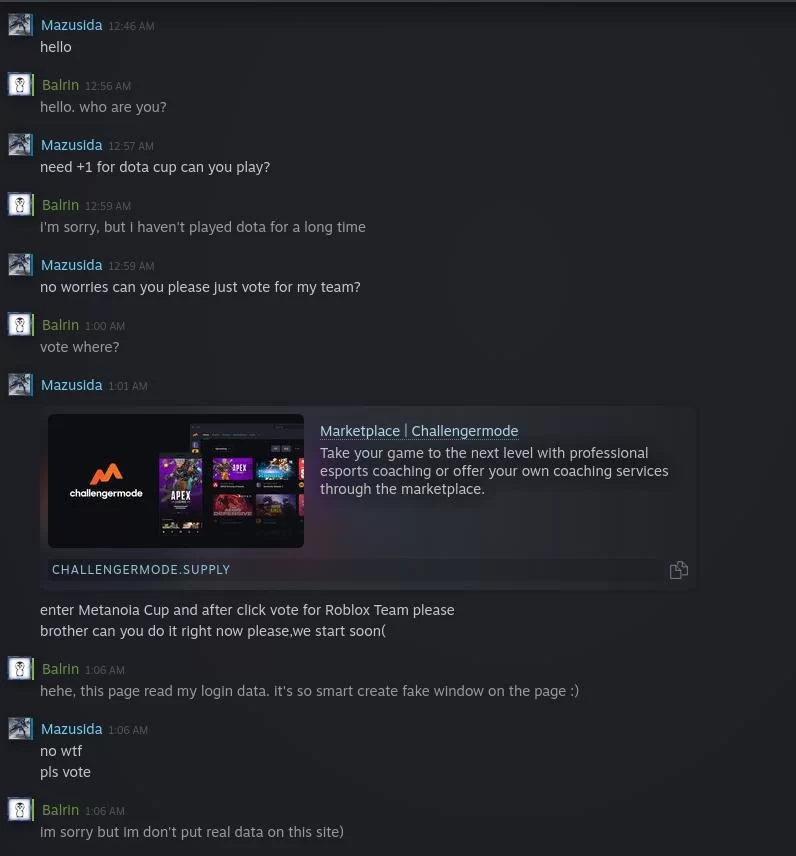
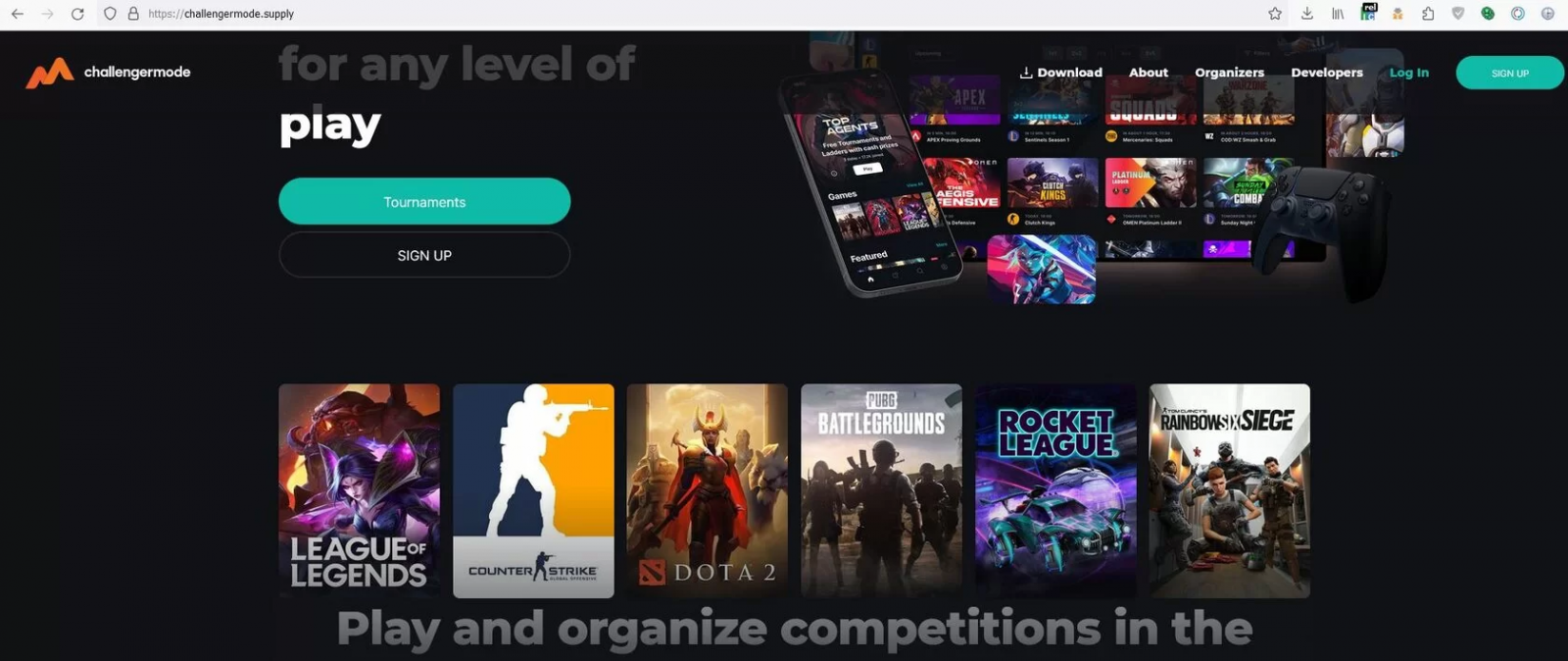
The links the phishing actors share will bring the targets to a phishing site for what appears to be an organization sponsoring and hosting esports competitions.
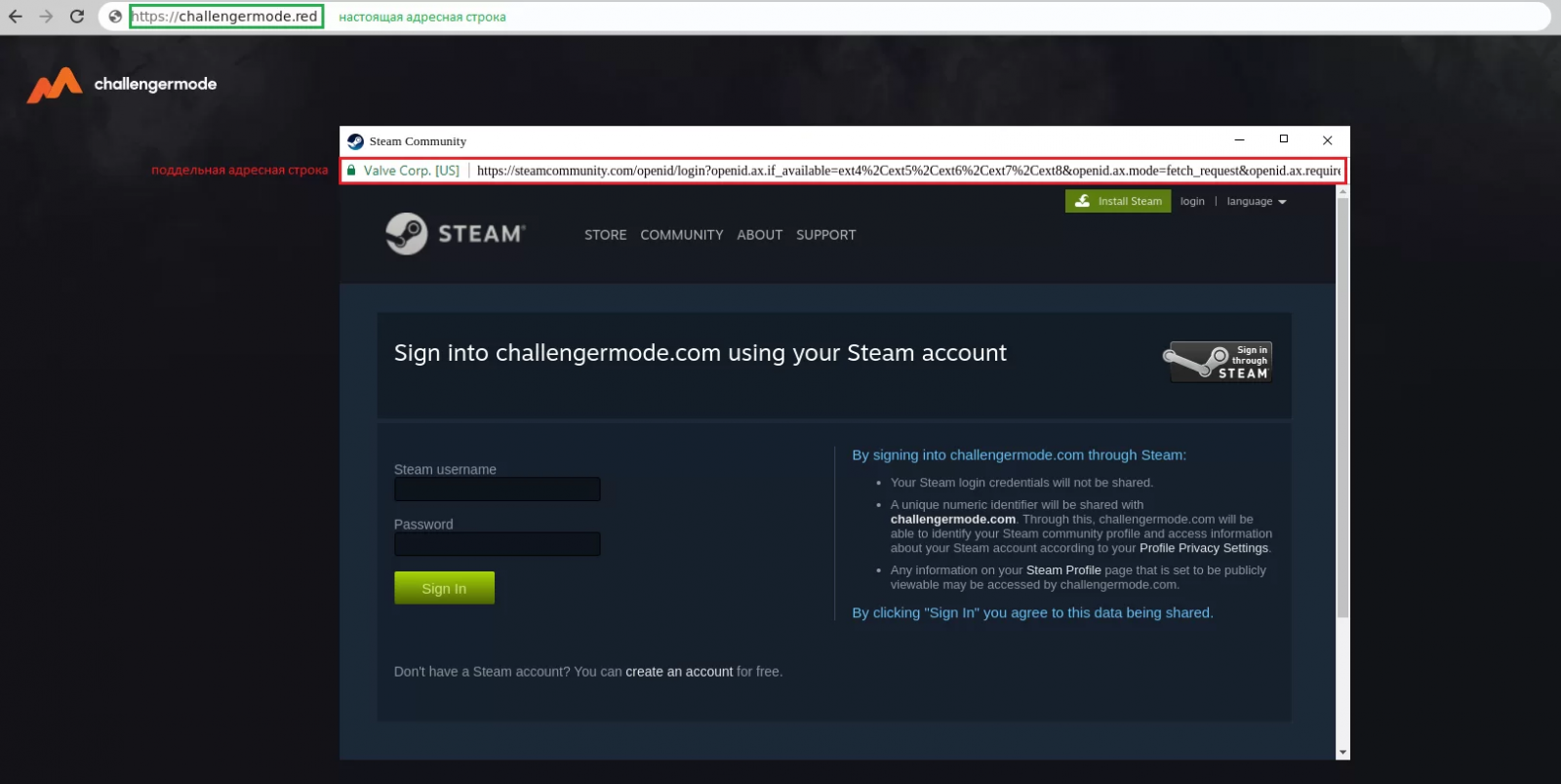
To join a team and play in a competition, the visitors are requested to log in via their Steam account. However, the new login page window isn’t an actual browser window overlaid over the existing website but rather a fake window created within the current page, making it very hard to spot as a phishing attack.
The landing pages even support 27 languages, detecting the language from the victim’s browser preferences and loading the correct one.
Once the victim enters their credentials, a new form prompts them to enter the 2FA code. If the second step is unsuccessful, an error message is displayed.
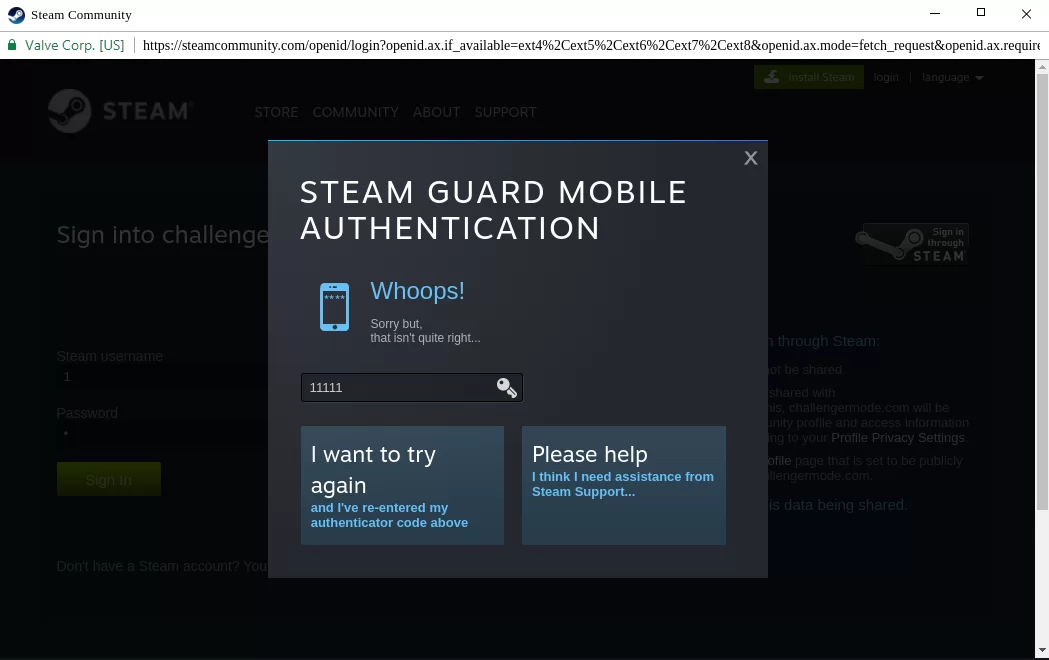
If the authentication is successful, the user is redirected to a URL specified by the C2, usually a legitimate address, to minimize the chances of the victim realizing the compromise.
At this point, the victim’s credentials have already been stolen and sent to the threat actors. In similar attacks, the threat actors quickly hijack the Steam accounts, changing passwords and email addresses to make it more difficult for the victims to regain control over their accounts.
Trending: Security Engineer vs. Software Engineer
Trending: Recon Tool: ZenBuster
How to spot a Browser-in-the-Browser attack
In all Browser-in-the-Browser phishing cases, the URL in the phishing window is the legitimate one, as the threat actors are free to display whatever they want since it’s not a browser window but merely a render of one.
The same applies to the SSL certificate lock symbol, indicating an HTTPS connection, creating a false sense of security for the victims.
Even worse, the phishing kit allows users to drag the fake window around, minimize it, maximize it, and close it, making it very difficult to spot as a fake browser-in-the-browser window.
As the technique requires JavaScript, blocking JS scripts aggressively would prevent the fake login from being displayed. However, most people do not block scripts as it would break many popular websites.
In general, be very wary of direct messages received on Steam, Discord, or other game-related platforms, and avoid following links sent by users you do not know.
Are u a security researcher? Or a company that writes articles or write ups about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing?
If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com












