Android banking malware infects 300,000 Google Play users

Reading Time: 1 Minute
Malware campaigns distributing Android trojans that steals online bank credentials have infected almost 300,000 devices through malicious apps pushed via Google’s Play Store.
The stolen credentials are then sent back to the attacker’s servers, where they are collected to be sold to other threat actors or used to steal cryptocurrency and money from victims’ accounts.
Evolving tactics to evade detection
In a new report by ThreatFabric, researchers explain how they discovered four different malware dropper campaigns distributing banking trojans on the Google Play Store.
While threat actors infiltrating the Google Play Store with Android banking trojans are nothing new, recent changes to Google’s policies and increased policing have forced threat actors to evolve their tactics to evade detection.
This evolution includes creating small realistic-looking apps that focus on common themes such as fitness, cryptocurrency, QR codes, and PDF scanning to trick users into installing the app. Then, to add further legitimacy to the apps, the threat actors create websites that fit the theme of the app to help pass reviews by Google.
See Also: Complete Offensive Security and Ethical Hacking Course
Furthermore, ThreatFabric has seen these apps only being distributed to specific regions or at later dates to further evade detection by Google and antivirus vendors.
“This policing by Google has forced actors to find ways to significantly reduce the footprint of dropper apps. Besides improved malware code efforts, Google Play distribution campaigns are also more refined than previous campaigns,” ThreatFabric researchers explain in their new report.
“For example, by introducing carefully planned small malicious code updates over a longer period in Google Play, as well as sporting a dropper C2 backend to fully match the theme of the dropper app (for example a working Fitness website for a workout focused app).”
However, once these “dropper” apps are installed, they will silently communicate with the threat actor’s server to receive commands. When ready to distribute the banking trojan, the threat actor’s server will tell the installed app to perform a fake “update” that “drops” and launches the malware on the Android device.
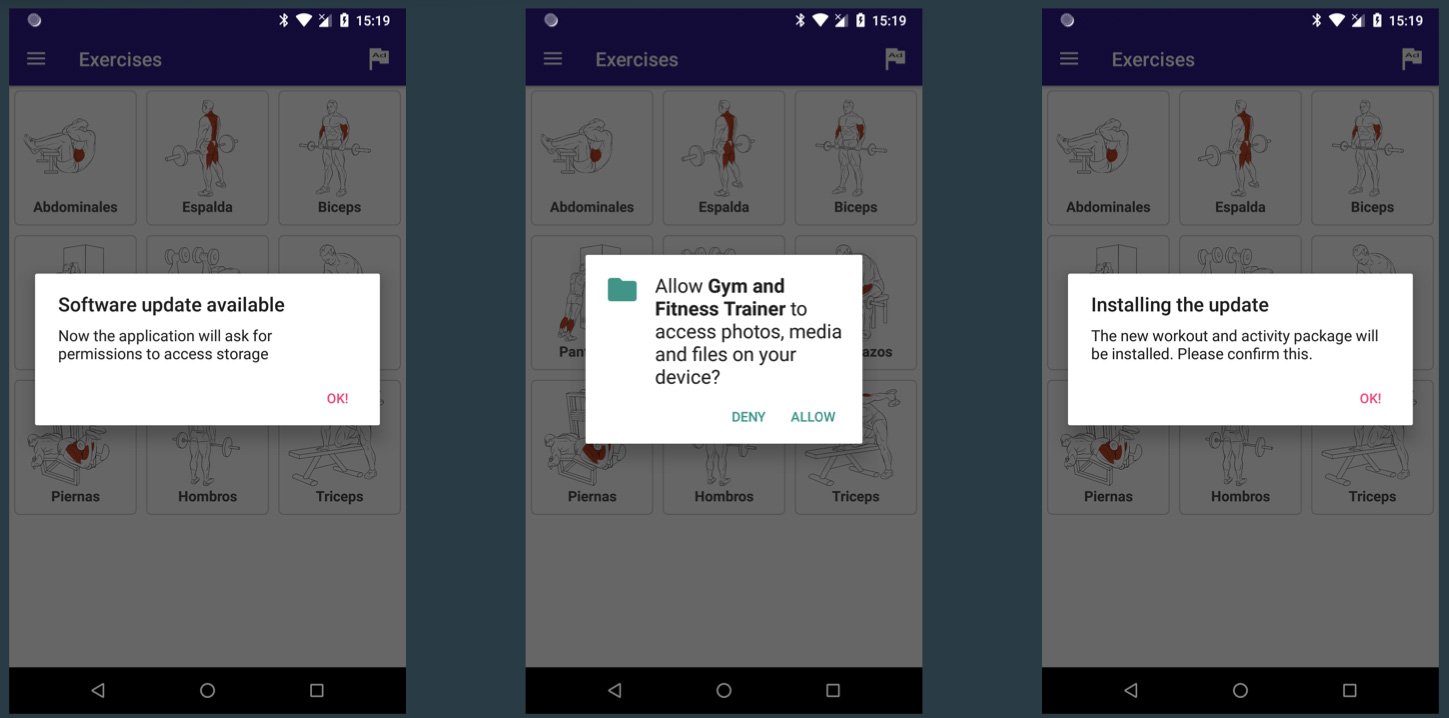
Source: ThreatFabric
See Also: New Windows zero-day with public exploit lets you become an admin
16 apps infect 300,000 devices
Since July 2021, ThreatFabric has these fake apps dropping four different banking trojans named ‘Alien’, ‘Hydra’, ‘Ermac’, and and ‘Anatsa’ through sixteen different apps.
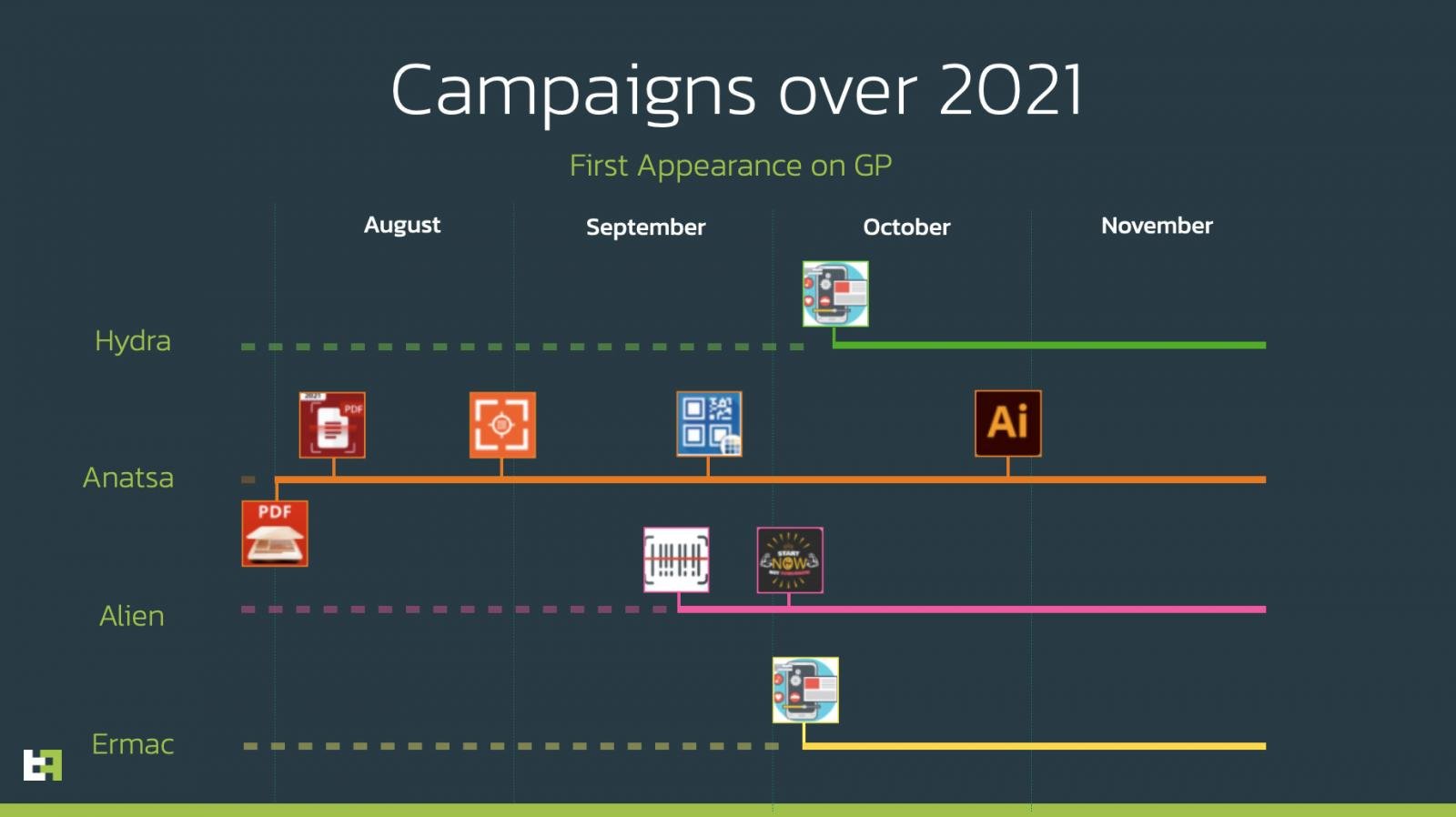
Timeline of malware campaigns on Google Play
Source: ThreatFabric
The “dropper” apps known to be used during these malware distribution campaigns are:
- Two Factor Authenticator
- Protection Guard
- QR CreatorScanner
- Master Scanner
- QR Scanner 2021
- QR Scanner
- PDF Document Scanner – Scan to PDF
- PDF Document Scanner
- PDF Document Scanner Free
- CryptoTracker
- Gym and Fitness Trainer
Other malicious apps seen installed by the above droppers and their associated banking trojans are:
- Master Scanner Live (Alien trojan)
- Gym and Fitness Trainer (Alien trojan)
- PDF AI : TEXT RECOGNIZER (Anatsa trojan)
- QR CreatorScanner (Hydra trojan)
- QR CreatorScanner (Ermac trojan)
See Also: Offensive Security Tool: Hashcat
See Also: Hacking stories – Operation Troy – How researchers linked the cyberattacks
Google has since removed all of these malicious apps from the Play Store and you should also immediately remove them from your Android device if you have any of them installed.
If you have installed any of the above apps, you should immediately remove them from your Android device.
Furthermore, due to the evolving techniques used by Android malware developers, users must pay more attention to the permissions requested by apps and block the install if they seem overly broad.
Source: www.bleepingcomputer.com
(Click Link)












