Malware Campaign Hijacks eScan Antivirus Updates for Backdoor and Cryptocurrency Miner Distribution
Avast researchers recently uncovered a troubling malware campaign that capitalized on the update mechanism of the eScan antivirus software to disseminate backdoors and cryptocurrency miners across targeted systems. This discovery sheds light on a sophisticated attack method employed by threat actors, potentially linked to North Korea’s AP Kimsuky group.
The campaign leveraged vulnerabilities in eScan’s update process, enabling malicious actors to execute a man-in-the-middle attack, intercepting legitimate updates and substituting them with compromised packages. Avast promptly alerted eScan and the Indian CERT, leading to the flaw’s resolution on July 31, 2023, after persisting for five years.
The infection sequence commenced with the compromised eScan updater, unwittingly fetching a malicious update package, courtesy of the attackers’ manipulation during transmission. Once installed, this package facilitated the injection of rogue DLLs, allowing for the execution of shellcodes and intermediary loaders, all under the guise of eScan’s legitimacy.

See Also: So, you want to be a hacker?
Offensive Security, Bug Bounty Courses
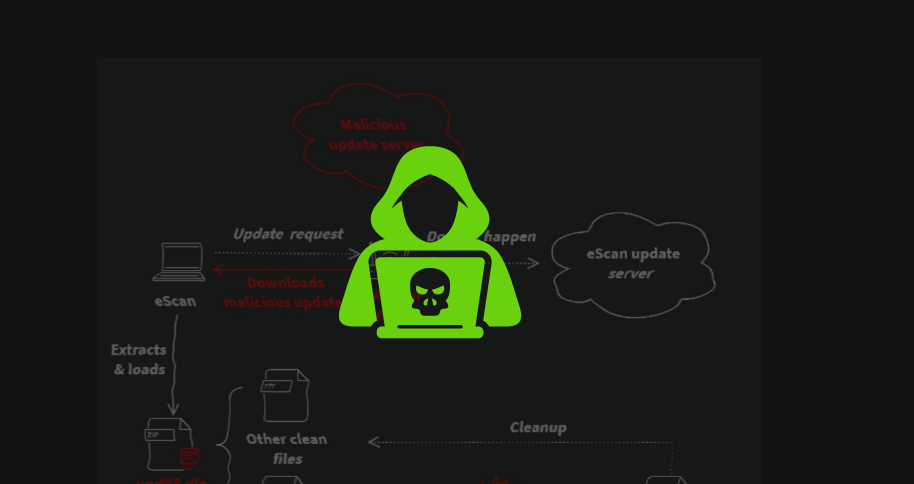
The stages of the infection chain described in the malware campaign exploiting the eScan antivirus update mechanism:
-
eScan Antivirus Updater Triggers Update: The eScan antivirus updater initiates an update process, intending to fetch the latest update package from the designated server.
-
Malicious Replacement of Downloaded Package: Due to the absence of HTTPS encryption, attackers conduct a man-in-the-middle (MitM) attack, substituting the legitimate update package with a malicious one during transmission.
-
Download and Unpack Malicious Package: The compromised eScan updater proceeds to download and unpack the malicious package named updll62.dlz, oblivious to its tainted contents.
-
Sideloading of Malicious DLL: Inside the unpacked package resides a malicious DLL (commonly named version.dll) designed for sideloading by the eScan process. This DLL runs with the same privileges as the eScan process, ensuring persistence through subsequent system reboots.
-
Injection into Services.exe: If a mutex is absent (e.g., Mutex_ONLY_ME_V1), the malware searches for the services.exe process to inject its next-stage payload. This step ensures the continued operation of the malware within the system.
-
Cleanup of Update Package: Post-injection, the malware conducts a cleanup operation, removing traces of the malicious update package to avoid detection.
Trending: Offensive Security Tool: 403jump
An intriguing aspect of this campaign is the deployment of GuptiMiner, a highly sophisticated threat aiming to infiltrate corporate networks. GuptiMiner orchestrates its own DNS infrastructure, evading traditional detection methods by operating outside typical DNS protocols.
Furthermore, GuptiMiner’s payload includes XMRig, a cryptocurrency miner, hinting at diversionary tactics. Avast’s researchers noted potential connections between this campaign and information-stealing operations attributed to the Kimsuky group.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: securityaffairs.com