MSI accidentally breaks Secure Boot for hundreds of motherboards

Reading Time: 3 Minutes
Over 290 MSI motherboards are reportedly affected by an insecure default UEFI Secure Boot setting settings that allows any operating system image to run regardless of whether it has a wrong or missing signature.
This discovery comes from a Polish security researcher named Dawid Potocki, who claims that he did not receive a response despite his efforts to contact MSI and inform them about the issue.
The issue, according to Potocki, impacts many Intel and AMD-based MSI motherboards that use a recent firmware version, affecting even brand-new MSI motherboard models.
See Also: So you want to be a hacker?
Offensive Security, Bug Bounty Courses
UEFI Secure Boot
Secure Boot is a security feature built into the firmware of UEFI motherboards that ensures only trusted (signed) software can execute during the boot process.
“When the PC starts, the firmware checks the signature of each piece of boot software, including UEFI firmware drivers (also known as Option ROMs), EFI applications, and the operating system,” explains Microsoft in an article about Secure Boot.
“If the signatures are valid, the PC boots, and the firmware gives control to the operating system.”
To validate the safety of boot loaders, OS kernels, and other essential system components, Secure Boot checks the PKI (public key infrastructure) that authenticates the software and determines its validity on every boot.
If the software is unsigned or its signature has changed, possibly because it was modified, the boot process will be stopped by Secure Boot to protect the data stored on the computer.
This security system is designed to prevent UEFI bootkits/rootkits (1, 2, 3) from launching on the computer and to warn users that their operating system has been tampered with after the vendor shipped the system.
Trending: Offensive Security Tool: Freeze
Default MSI settings cause insecure boots
Potocki claims that MSI’s firmware update version’ 7C02v3C,’ released on January 18, 2022, changed a default Secure Boot setting on MSI motherboards so that the system will boot even if it detects security violations.
“I decided to setup Secure Boot on my new desktop with the help of sbctl. Unfortunately, I have found that my firmware was accepting every OS image I gave it, no matter if it was trusted or not,” explains the researcher in his writeup.
“As I have later discovered on 2022-12-16, it wasn’t just broken firmware; MSI had changed their Secure Boot defaults to allow booting on security violations(!!).”
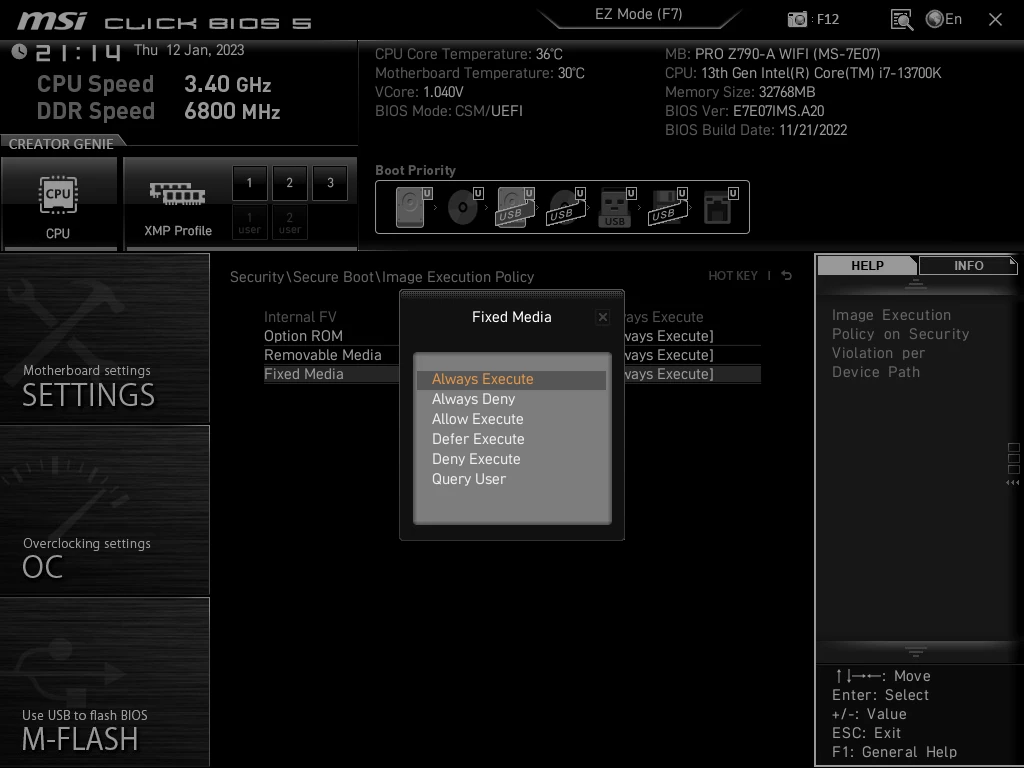
This change was to mistakenly set the “Image Execution Policy” setting in the Firmware to “Always Execute” by default, allowing any image to boot the device as normal.

Source: dawidpotocki.com
As you can see from the image above, even though Secure Boot is enabled, it’s ‘Image Execution Policy’ setting is set to ‘Always Execute’, allowing the system to boot even if there are security violations.
This effectively breaks the Secure Boot feature as untrusted images can still be used to boot the device
Potocki explains that users should set the Execution Policy to “Deny Execute” for “Removable Media” and “Fixed Media,” which should only allow signed software to boot.
The researcher says MSI never documented the change, so he had to trace back the introduction of the insecure default using IFR (UEFI Internal Form Representation) to extract configuration options information.
Potocki then used this information to determine which MSI motherboards were impacted by the issue. A complete list of the over 290 motherboards affected by this insecure setting is available on GitHub.
If you’re using an MSI motherboard in that list, go over to BIOS settings and check that the “Image Execution Policy” is set to a safe option.
If you haven’t upgraded your motherboard firmware since January 2022, the introduction of a bad default shouldn’t be a reason to postpone it any further, as software updates contain important security fixes.
BleepingComputer has contacted MSI to request a comment on the above and whether they plan to change the default setting via a new update, but we are still waiting to receive a response.
Are u a security researcher? Or a company that writes articles or write ups about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing?
If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com