Oracle Breach Exposes Millions of Stolen Credentials from Legacy Cloud System

See Also: So, you want to be a hacker?
Offensive Security, Bug Bounty Courses
Oracle Denies Cloud Breach as Leaked Data Circulates
Despite mounting evidence, Oracle has consistently denied that Oracle Cloud was breached, telling BleepingComputer:
“There has been no breach of Oracle Cloud. The published credentials are not for the Oracle Cloud.”
However, archived URLs show that the attacker uploaded files to Oracle’s servers, a claim Oracle has not addressed. Multiple companies have also confirmed that samples of leaked LDAP data, email addresses, and usernames are authentic.
Security experts believe Oracle is using wordplay to downplay the breach. Cybersecurity analyst Kevin Beaumont explains:
“Oracle rebadged old Oracle Cloud services to be Oracle Classic. Oracle Classic has the security incident.”
While technically true, the affected services were still Oracle-managed cloud platforms, raising questions about transparency.
Oracle Health Breach: Patient Data Stolen, Hospitals Extorted
Separately, Oracle has notified clients about a breach at Oracle Health (formerly Cerner), which has compromised patient data across multiple U.S. hospitals.
How the Oracle Health Breach Unfolded:
✔ Attack detected on February 20, 2025
✔ Hackers used stolen customer credentials to access legacy data migration servers
✔ Impacted hospitals are now being extorted for millions
A threat actor known as “Andrew” is demanding cryptocurrency payments in exchange for not leaking sensitive patient data. The hacker has even created public websites to pressure hospitals into paying the ransom.
Trending: Offensive Security Tool: DS Viper
Oracle Faces Scrutiny as Investigations Continue
Despite multiple attempts by journalists to obtain further comments, Oracle has not publicly disclosed the full impact of either breach.
With CrowdStrike, the FBI, and cybersecurity firms now investigating, Oracle may soon be forced to provide clearer answers about the true scale of these breaches.
For now, impacted users and organizations are urged to:
✔ Reset passwords linked to Oracle Cloud and Oracle Health
✔ Enable multi-factor authentication (MFA) for all accounts
✔ Monitor for suspicious activity related to compromised credentials
With stolen credentials now in circulation, further attacks could be imminent.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com

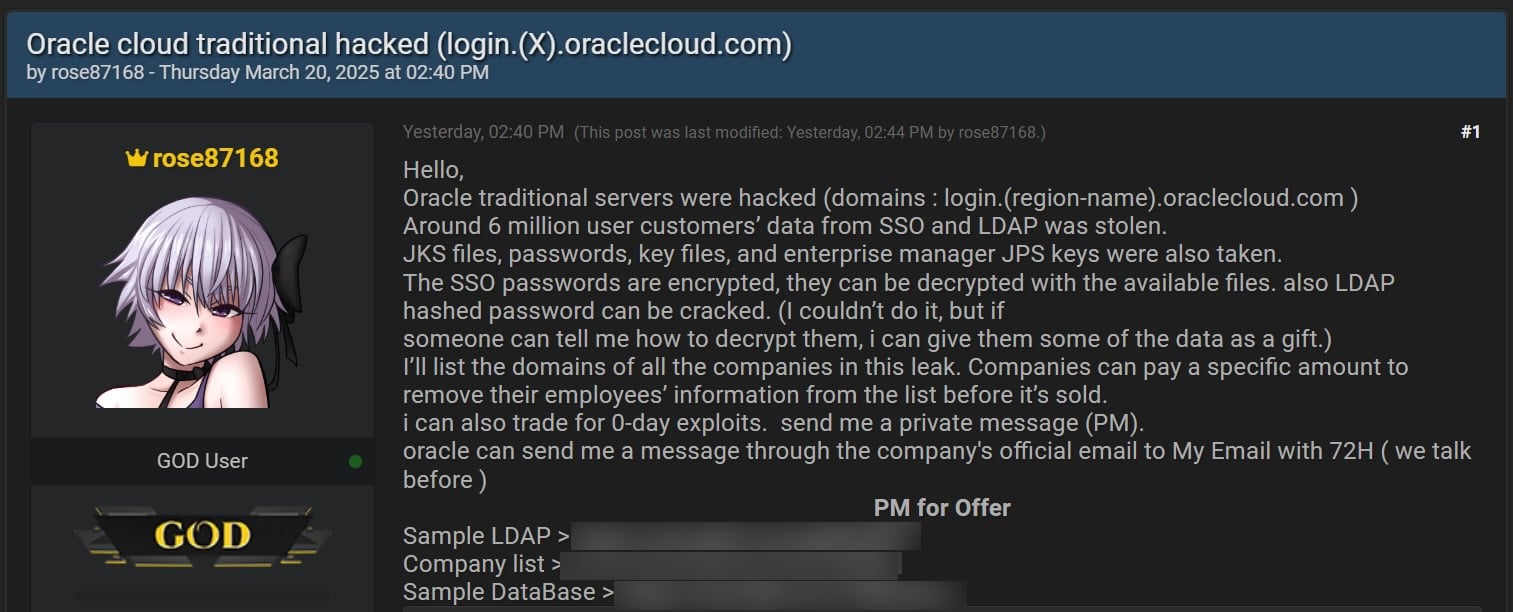 Threat actor selling data allegedly stolen from Oracle Cloud (BleepingComputer)
Threat actor selling data allegedly stolen from Oracle Cloud (BleepingComputer)










