Twilio API Vulnerability: Threat Actors Access Millions of MFA User Numbers

Unsecured API Endpoint Exposes Millions of Authy Users
Twilio has confirmed that an unsecured API endpoint allowed threat actors to verify the phone numbers of millions of Authy multi-factor authentication users, potentially making them vulnerable to SMS phishing and SIM swapping attacks.
Authy App and Its Vulnerability
Authy is a mobile app that generates multi-factor authentication codes at websites where users have MFA enabled. In late June, a threat actor named ShinyHunters leaked a CSV text file containing what they claim are 33 million phone numbers registered with the Authy service.
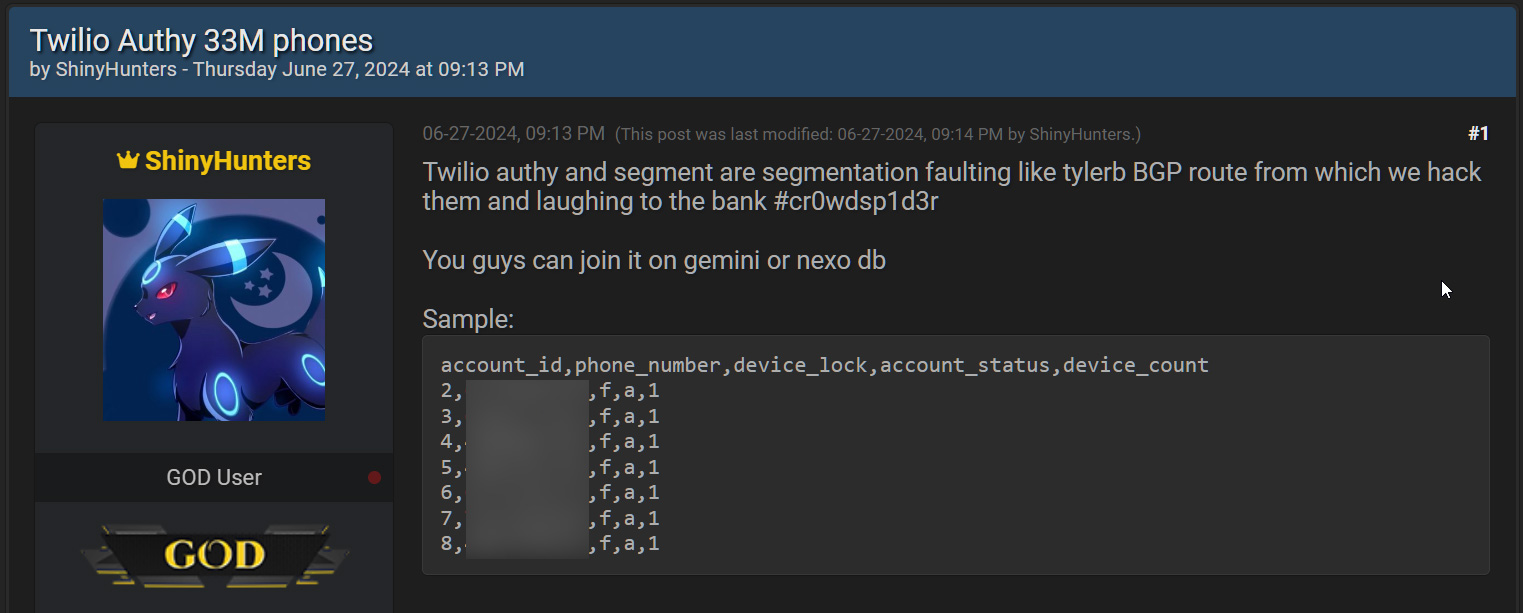 ShinyHunters sharing Twilio Authy data on a hacking forum
ShinyHunters sharing Twilio Authy data on a hacking forum
Source: BleepingComputer
The CSV file contains 33,420,546 rows, each including an account ID, phone number, an “over_the_top” column, account status, and device count.
Twilio’s Confirmation and Response
Twilio has now confirmed to BleepingComputer that the threat actors compiled the list of phone numbers using an unauthenticated API endpoint.
“Twilio has detected that threat actors were able to identify data associated with Authy accounts, including phone numbers, due to an unauthenticated endpoint. We have taken action to secure this endpoint and no longer allow unauthenticated requests,” Twilio told BleepingComputer.
“We have seen no evidence that the threat actors obtained access to Twilio’s systems or other sensitive data. As a precaution, we are requesting all Authy users to update to the latest Android and iOS apps for the latest security updates and encourage all Authy users to stay diligent and have heightened awareness around phishing and smishing attacks.”
See Also: So, you want to be a hacker?
Offensive Security, Bug Bounty Courses
History of Security Breaches
In 2022, Twilio disclosed it suffered breaches in June and August that allowed threat actors to breach its infrastructure and access Authy customer information.
Exploitation of Unsecured APIs
BleepingComputer has learned that the data was compiled by feeding a massive list of phone numbers into the unsecured API endpoint. If the number was valid, the endpoint would return information about the associated accounts registered with Authy.
Now that the API has been secured, it can no longer be abused to verify whether a phone number is used with Authy. This technique is similar to how threat actors abused unsecured Twitter and Facebook APIs to compile profiles of tens of millions of users.
Potential Risks and Threats
While the Authy scrape only contained phone numbers, they can still be advantageous to users looking to conduct smishing and SIM swapping attacks to breach accounts. ShinyHunters alludes to this in their post, suggesting that threat actors compare the list of phone numbers to those leaked in alleged Gemini and Nexo data breaches.
If matches are found, the threat actors could attempt to perform SIM swapping attacks or phishing attacks to breach the cryptocurrency exchange accounts and steal all the assets.
Trending: Offensive Security Tool: Genzai
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com