VMware urges admins to patch critical auth bypass bug immediately

Reading Time: 3 Minutes
VMware has warned admins today to patch a critical authentication bypass security flaw affecting local domain users in multiple products and enabling unauthenticated attackers to gain admin privileges.
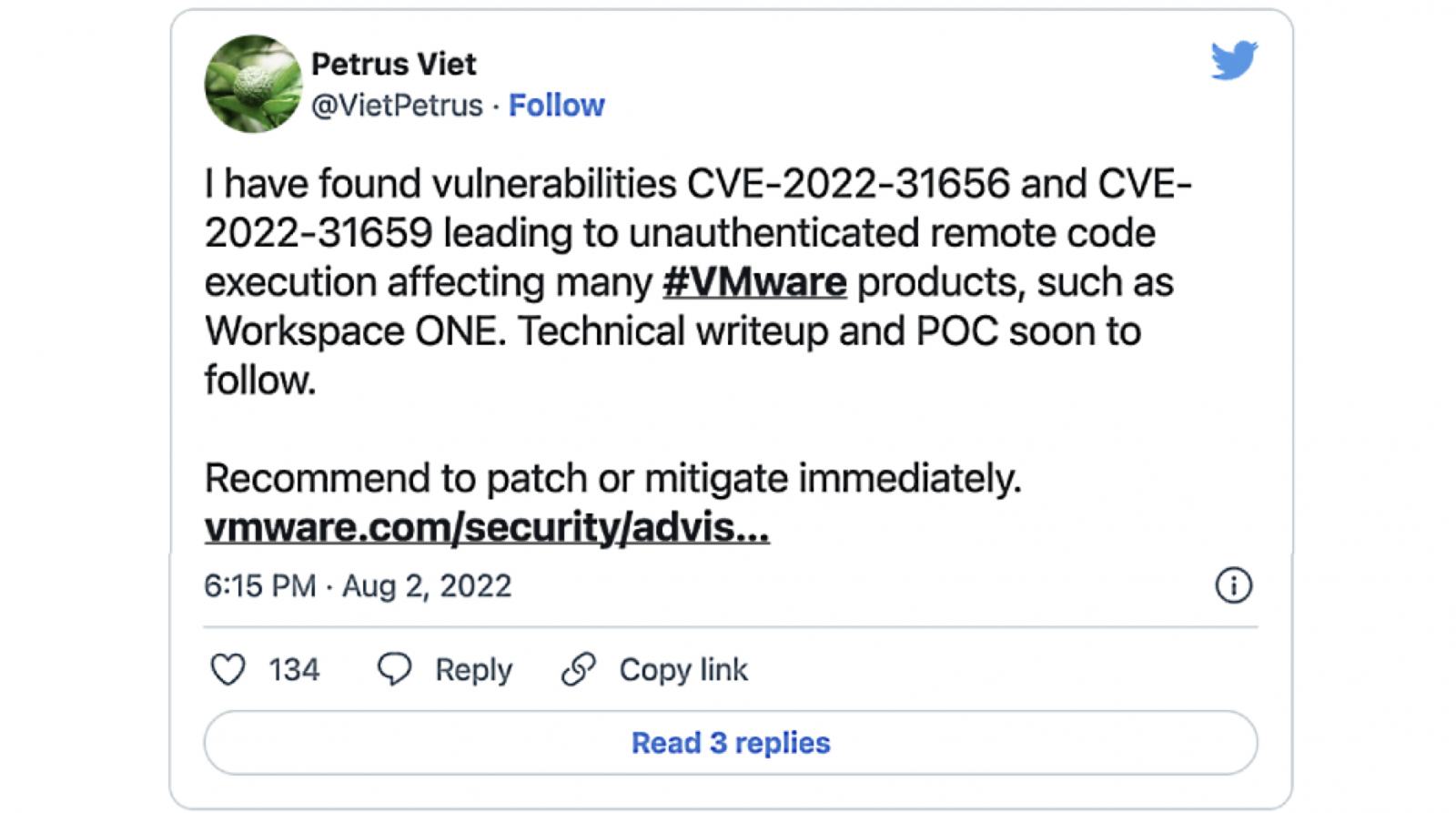
The flaw (CVE-2022-31656) was reported by Petrus Viet of VNG Security, who found that it impacts VMware Workspace ONE Access, Identity Manager, and vRealize Automation.
VMware evaluated the severity of this security vulnerability as critical, with a CVSSv3 base score of 9.8/10.
The company also patched multiple other security bugs enabling attackers to gain remote code execution (CVE-2022-31658, CVE-2022-31659, CVE-2022-31665) and escalate privileges to ‘root’ (CVE-2022-31660, CVE-2022-31661, CVE-2022-31664) on unpatched servers.
“It is extremely important that you quickly take steps to patch or mitigate these issues in on-premises deployments,” said Bob Plankers, Cloud Infrastructure Security & Compliance Architect at VMware.
“If your organization uses ITIL methodologies for change management, this would be considered an ’emergency’ change.”
See Also: So you want to be a hacker?
Complete Offensive Security and Ethical Hacking Course
Admins urged to patch immediately
“This critical vulnerability should be patched or mitigated immediately per the instructions in VMSA,” VMware warned.
“All environments are different, have different tolerance for risk, and have different security controls and defense-in-depth to mitigate risk, so customers must make their own decisions on how to proceed. However, given the severity of the vulnerability, we strongly recommend immediate action.”
The complete list of VMware products impacted by these vulnerabilities includes:
- VMware Workspace ONE Access (Access)
- VMware Workspace ONE Access Connector (Access Connector)
- VMware Identity Manager (vIDM)
- VMware Identity Manager Connector (vIDM Connector)
- VMware vRealize Automation (vRA)
- VMware Cloud Foundation
- vRealize Suite Lifecycle Manager
According to VMware, there is no evidence that the critical CVE-2022-31656 authentication bypass vulnerability is exploited in attacks.
VMware provides patch download links and detailed installation instructions on its knowledgebase website.
Workaround available
The company also shared a temporary workaround for customers who cannot patch their appliances against CVE-2022-31656 immediately.
Steps detailed by VMware require admins to disable all users except one provisioned administrator and log in via SSH to restart the horizon-workspace service.
However, VMware doesn’t recommend using this workaround and says the only way to address the CVE-2022-31656 auth bypass flaw fully is to patch the vulnerable products.
“The only way to remove the vulnerabilities from your environment is to apply the patches provided in VMSA-2022-0021. Workarounds, while convenient, do not remove the vulnerabilities, and almost always introduce additional complexities that patching would not,” VMware added.
“While the decision to patch or use the workaround is yours, VMware always strongly recommends patching as the simplest and most reliable way to resolve this type of issue.”
The company also provides a support document with a list of questions and answers regarding the critical bug patched today.
In May, VMware patched an almost identical critical vulnerability, another authentication bypass bug (CVE-2022-22972) found by Bruno López of Innotec Security in Workspace ONE Access, VMware Identity Manager (vIDM), and vRealize Automation.
Are u a security researcher? Or a company that writes articles or write ups about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing?
If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com