Digital Forensics Tool: MemProcFS-Analyzer

Reading Time: 3 Minutes
MemProcFS-Analyzer
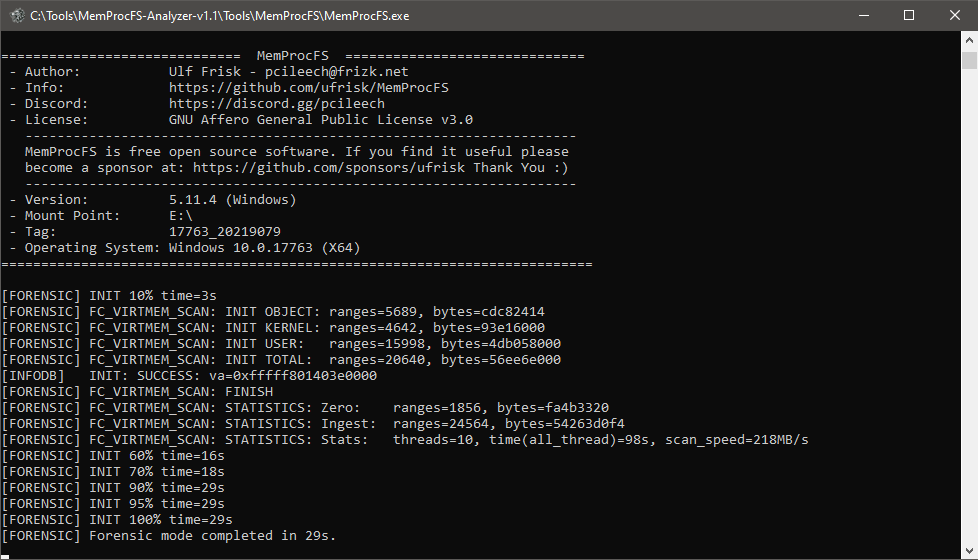
MemProcFS-Analyzer, developed by evild3ad, is a PowerShell script designed to streamline memory forensics by integrating with MemProcFS (Memory Process File System). It simplifies the process of analyzing memory snapshots (such as raw physical memory dumps or Microsoft crash dumps) by treating them like mounted disk images, making it easier to extract forensic artifacts and detect malicious activity.
See Also: So you want to be a hacker?
Offensive Security and Ethical Hacking Course
Features
- Fast and easy memory analysis!
- You can mount a memory snapshot (Raw Physical Memory Dump or Microsoft Crash Dump) like a disk image and handle the memory compression feature on Windows
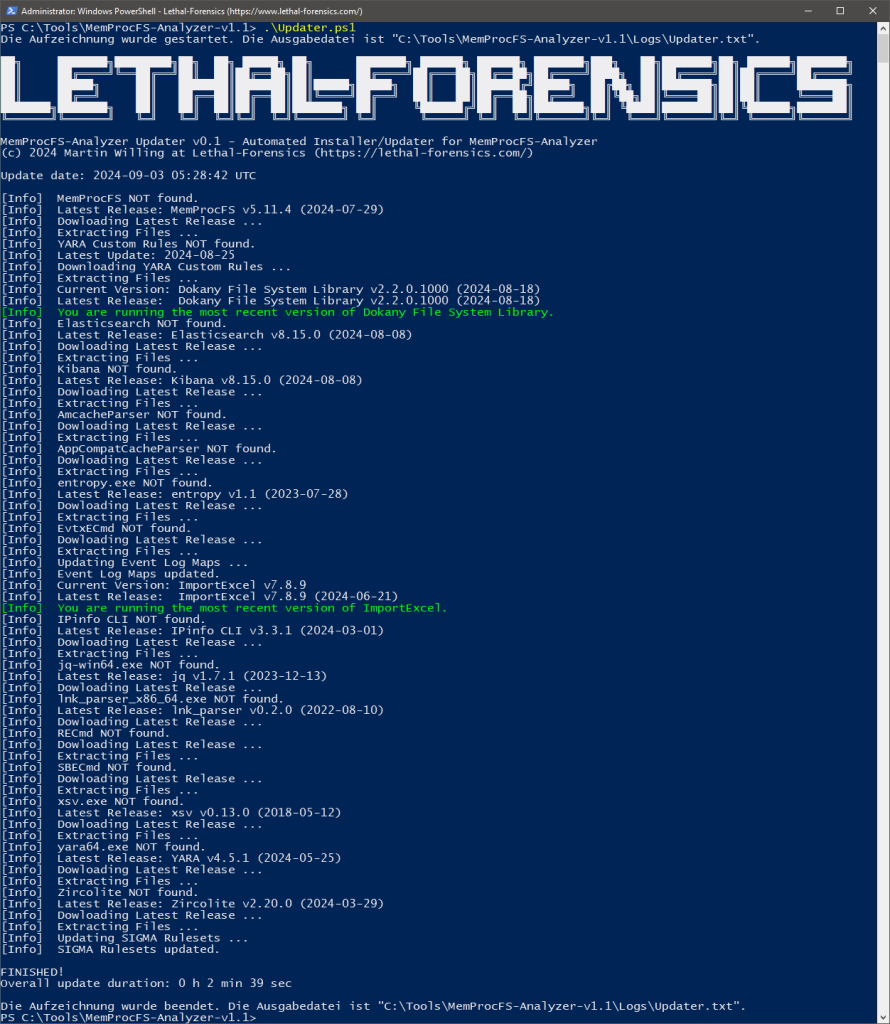
- Auto-Install of MemProcFS, AmcacheParser, AppCompatCacheParser, Elasticsearch, entropy, EvtxECmd, ImportExcel, IPinfo CLI, jq, Kibana, lnk_parser, RECmd, SBECmd, xsv, YARA, and Zircolite
- Auto-Update of MemProcFS, AmcacheParser, AppCompatCacheParser, Elasticsearch, entropy, EvtxECmd (incl. Maps), ImportExcel, IPinfo CLI, jq, Kibana, lnk_parser, RECmd, SBECmd, xsv, YARA, and Zircolite
- Update-Info when there’s a new version of ClamAV or a new Dokany File System Library Bundle available
- Pagefile Support
- OS Fingerprinting
- Scan w/ Custom YARA rules (incl. 391 rules by e.g. Chronicle and Elastic Security)
- Multi-Threaded scan w/ ClamAV for Windows
- Collection of infected files detected by ClamAV for further analysis (PW: infected)
- Collection of injected modules detected by MemProcFS PE_INJECT for further analysis (PW: infected)
- Extracting IPv4/IPv6
- IP2ASN Mapping and GeoIP w/ IPinfo CLI → Get your token for free at https://ipinfo.io/signup
- Checking for Suspicious Port Numbers
- Process Tree (TreeView) including complete Process Call Chain (Special thanks to Dominik Schmidt)
- Checking Processes for Unusual Parent-Child Relationships and Number of Instances
- Checking Processes for Unusual User Context
- Checking for Process Path Masquerading and Process Name Masquerading (Damerau Levenshtein Distance)
- Web Browser History (Google Chrome, Microsoft Edge and Firefox)
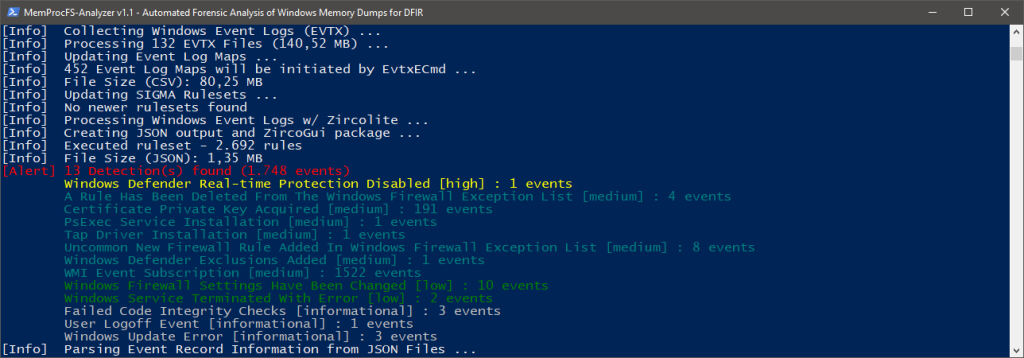
- Extracting Windows Event Log Files and processing w/ EvtxECmd → Timeline Explorer (EZTools by Eric Zimmerman)
- Event Log Overview
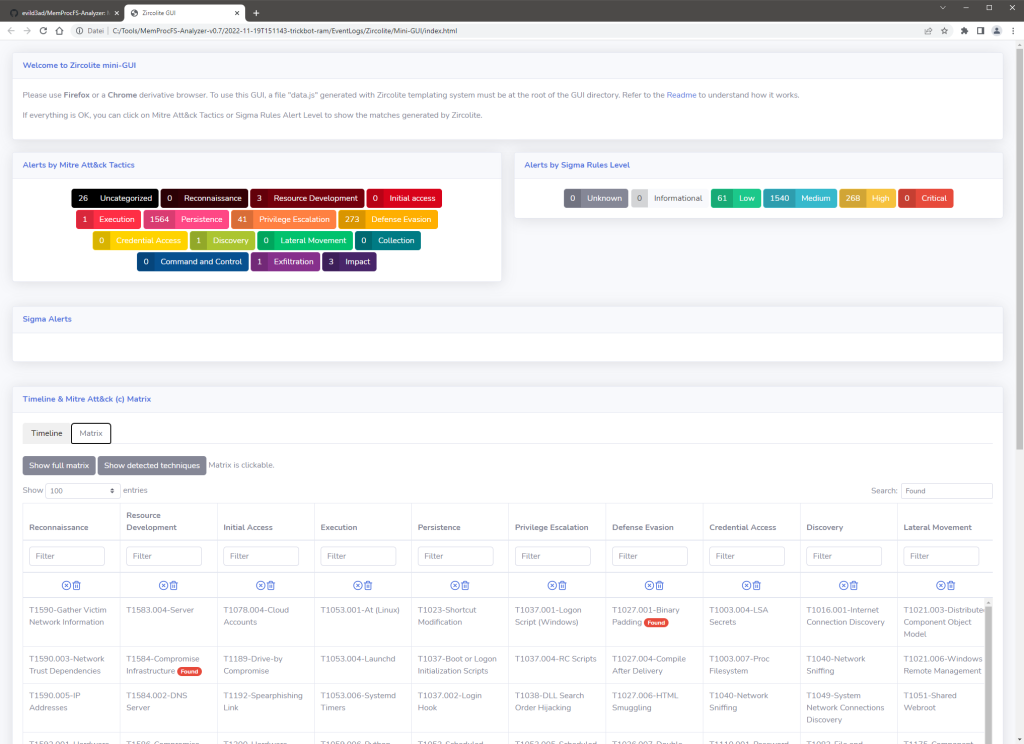
- Processing Windows Event Logs w/ Zircolite – A standalone SIGMA-based detection tool for EVTX
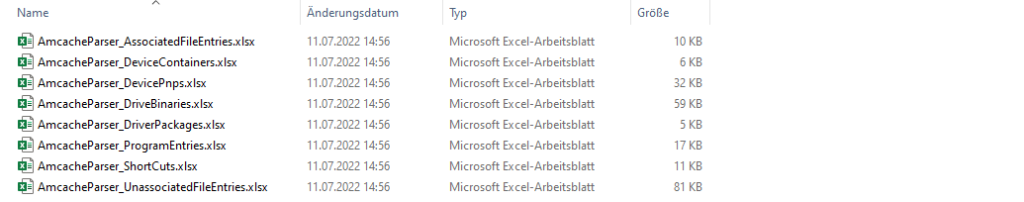
- Analyzing extracted Amcache.hve w/ AmcacheParser (EZTools by Eric Zimmerman)
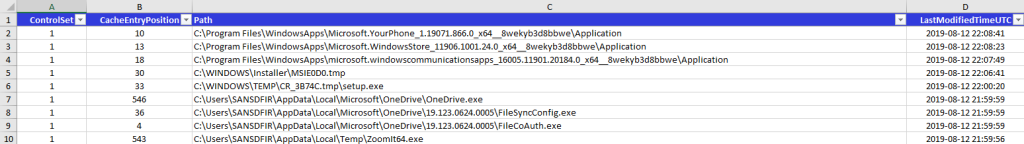
- Analyzing Application Compatibility Cache aka ShimCache w/ AppCompatcacheParser (EZTools by Eric Zimmerman)
- Analyzing Syscache w/ RECmd (EZTools by Eric Zimmerman)
- Analyzing UserAssist Artifacts w/ RECmd (EZTools by Eric Zimmerman)
- Analyzing ShellBags Artifacts w/ RECmd (EZTools by Eric Zimmerman)
- Simple Prefetch View (based on Forensic Timeline)
- Analyzing Auto-Start Extensibility Points (ASEPs) w/ RECmd (EZTools by Eric Zimmerman)
- Analyzing RecentDocs, Office Trusted Document w/ RECmd (EZTools by Eric Zimmerman)
- Analyzing Registry w/ RECmd DFIR Batch File (DFIR Batch File by Andrew Rathbun)
- Analyzing Metadata of Recovered Process Modules (experimental)
- Analyzing Microsoft Protection Logs (experimental)
- Extracting Windows Shortcut Files (LNK)
- Hunting Malicious Windows Shortcut Files (LNK)
- Integration of PowerShell module ImportExcel by Doug Finke
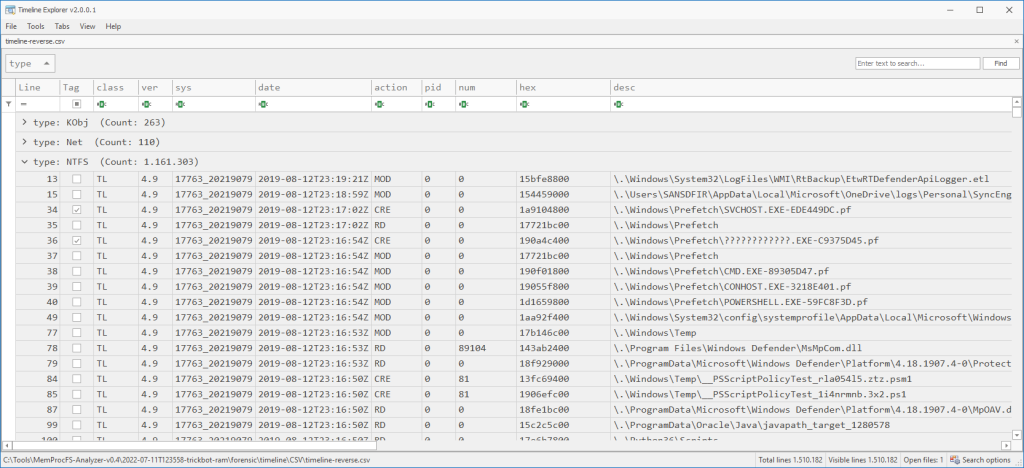
- CSV output data for analysis w/ Timeline Explorer (e.g. timeline-reverse.csv, findevil.csv, web.csv)
- Collecting Evidence Files (Secure Archive Container → PW: MemProcFS)
- Offline-Mode
- and much more
See Also: Digital Forensics Tool: Elyzer
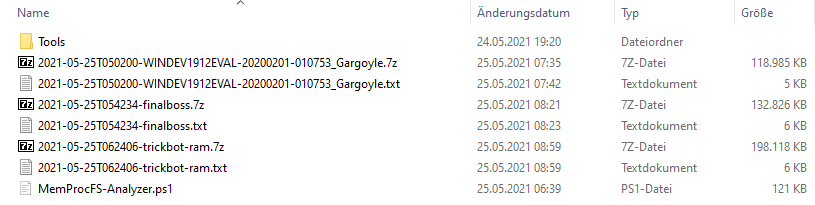
Usage
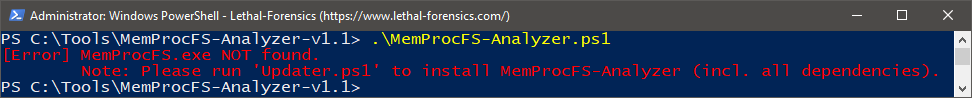
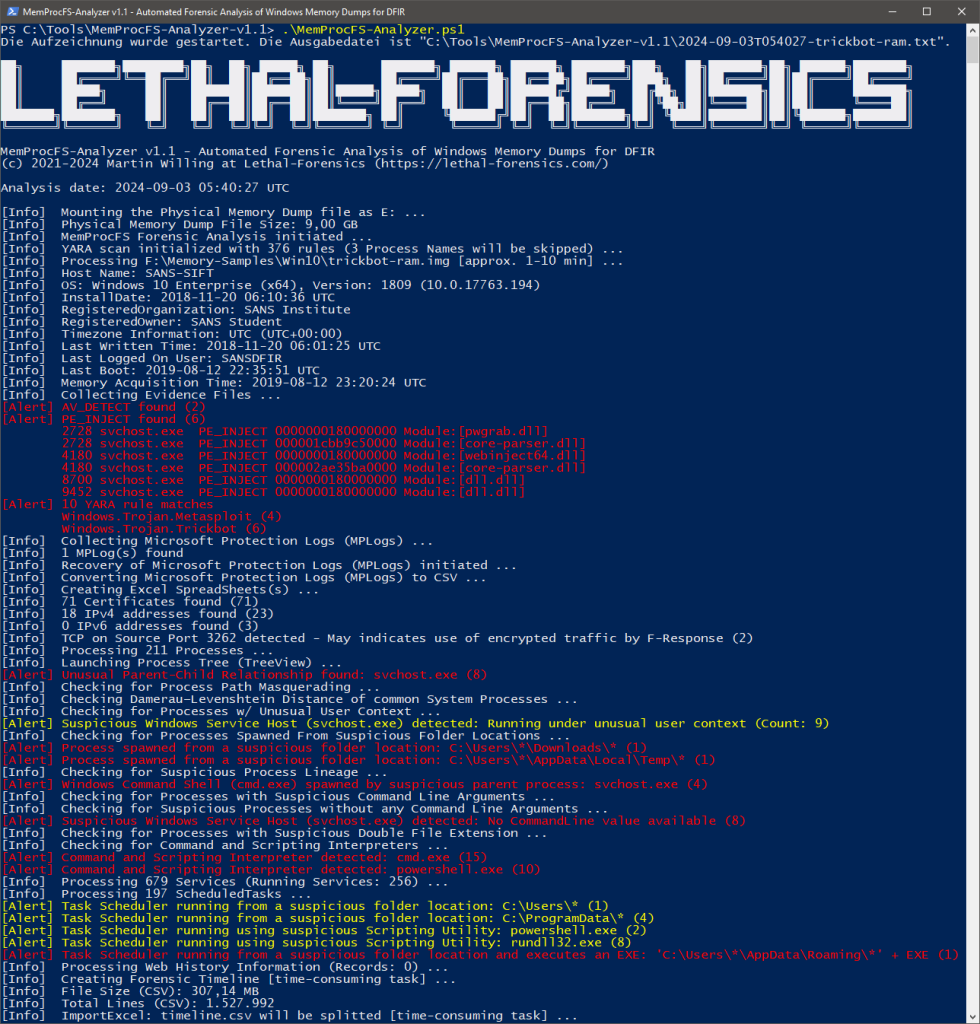
Launch Windows PowerShell (or Windows PowerShell ISE or Visual Studio Code w/ PSVersion: 5.1) as Administrator and open/run MemProcFS-Analyzer.ps1.
Fig 1: MemProcFS-Analyzer.ps1 (First Run) → Updater.ps1
Fig 2: Updater.ps1 automatically installs/updates all dependencies (First Run)
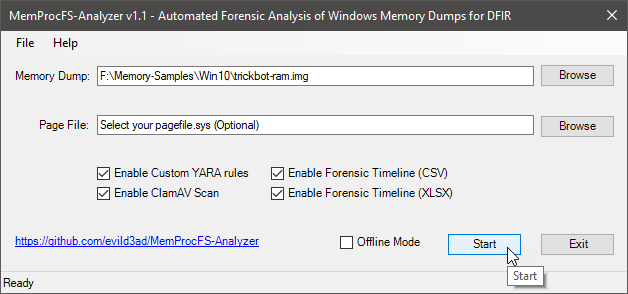
Fig 3: Select your Memory Snapshot and select your pagefile.sys (Optional)
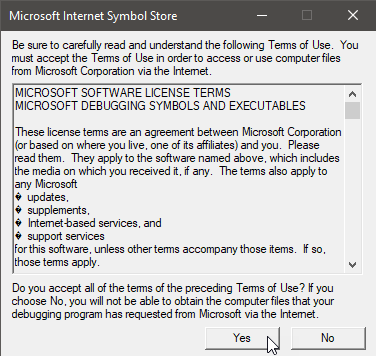
Fig 4: Accept Terms of Use (First Run)
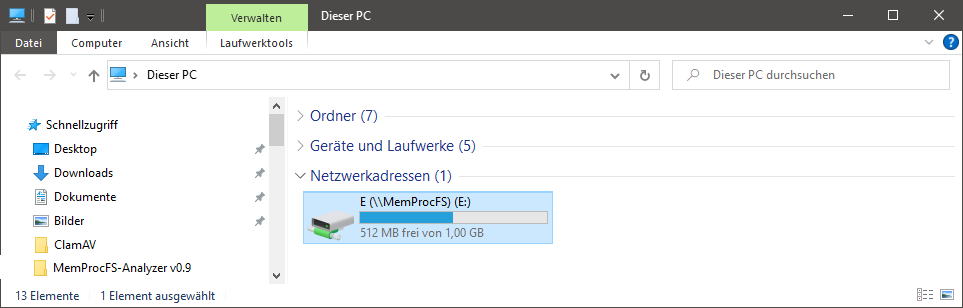
Fig 6: You can investigate the mounted memory dump by exploring drive letter
Fig 7: FindEvil feature and additional analytics
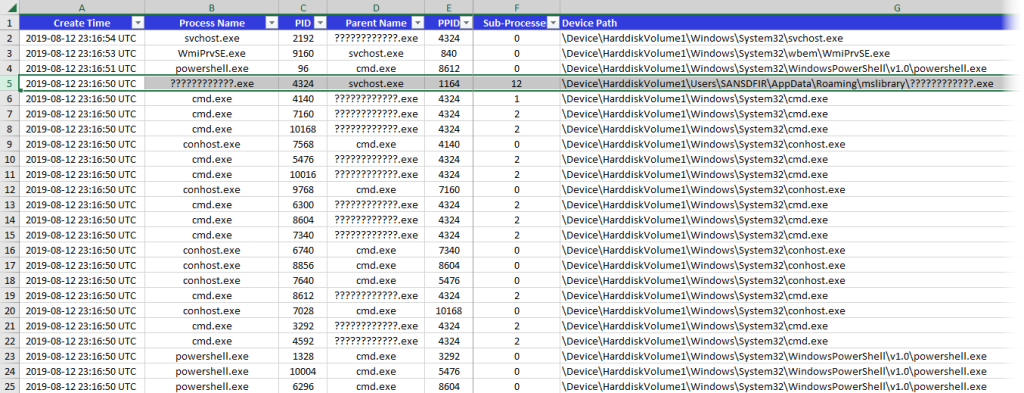
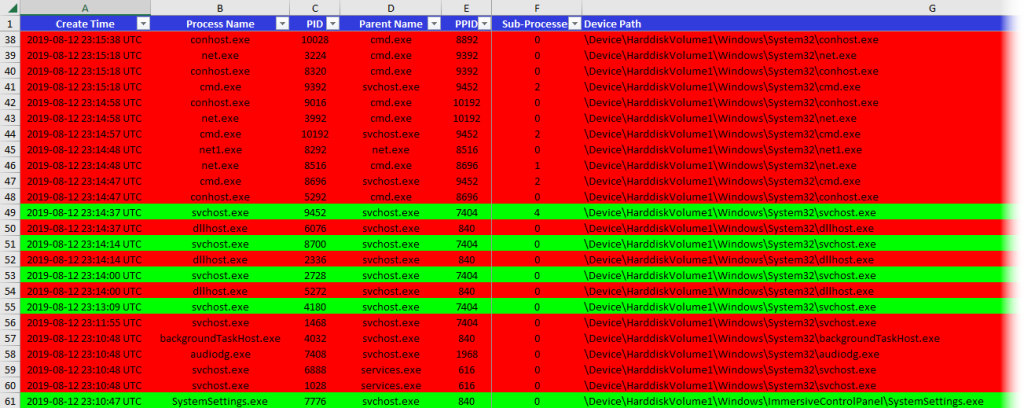
Fig 8: Processes
Fig 9: Running and Exited Processes
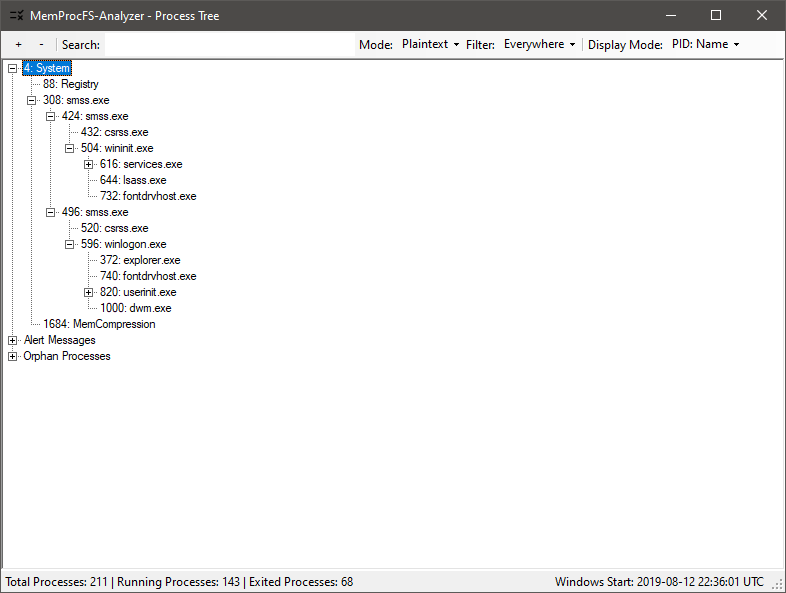
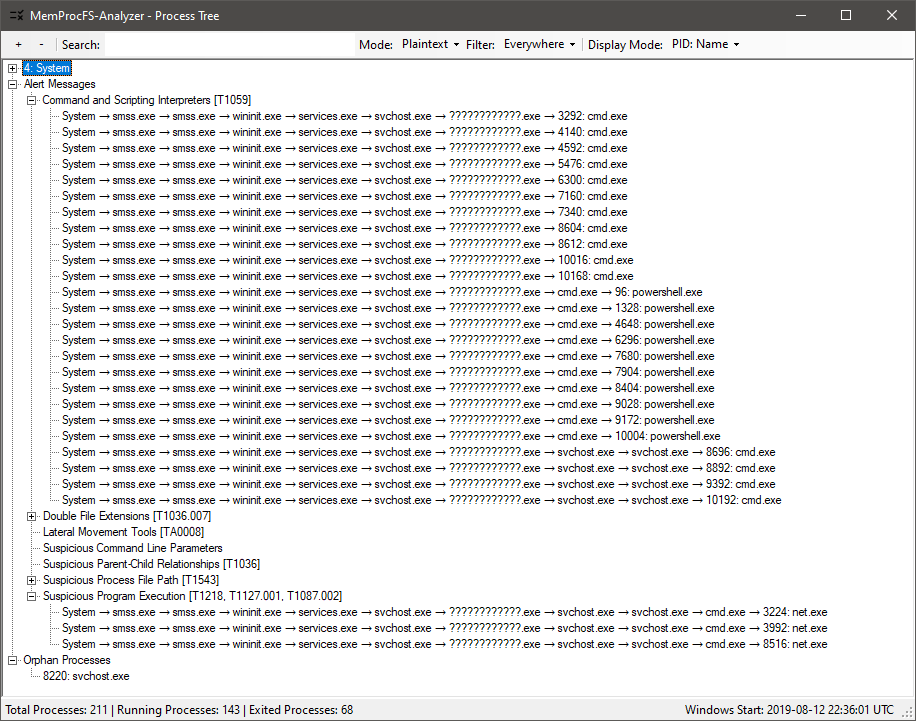
Fig 10: Process Tree (GUI)
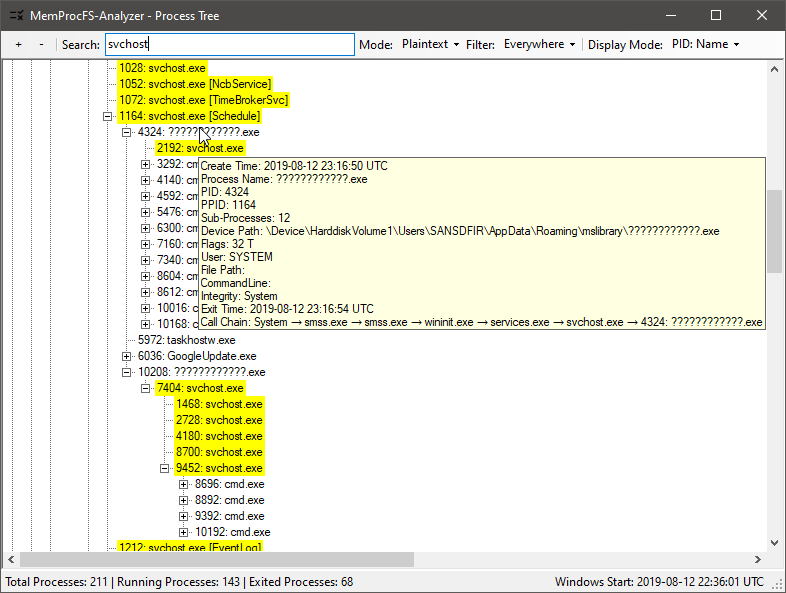
Fig 11: Checking Process Tree (to find anomalies)
Fig 12: Process Tree: Alert Messages w/ Process Call Chain
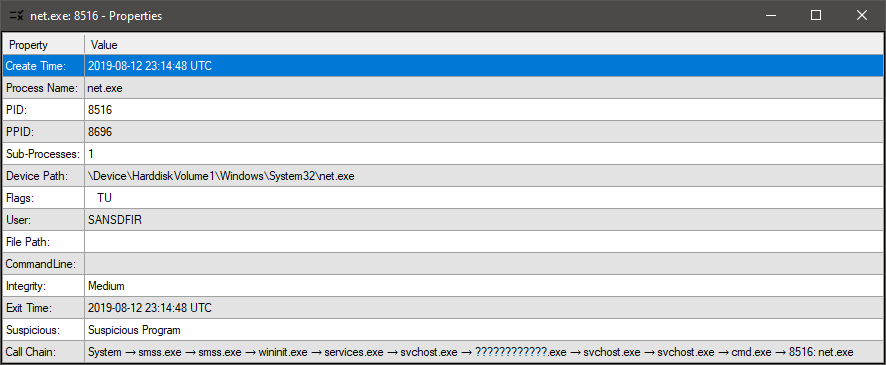
Fig 13: Process Tree: Properties View → Double-Click on a process or alert message
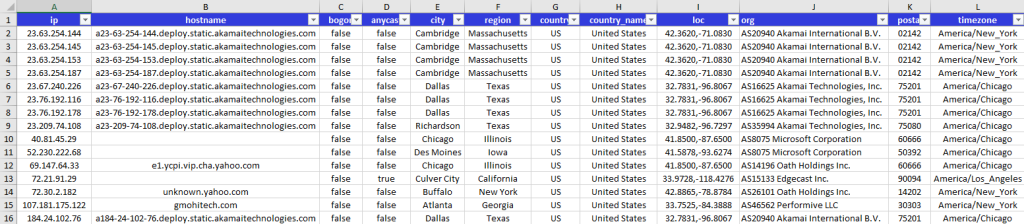
Fig 14: GeoIP w/ IPinfo.io
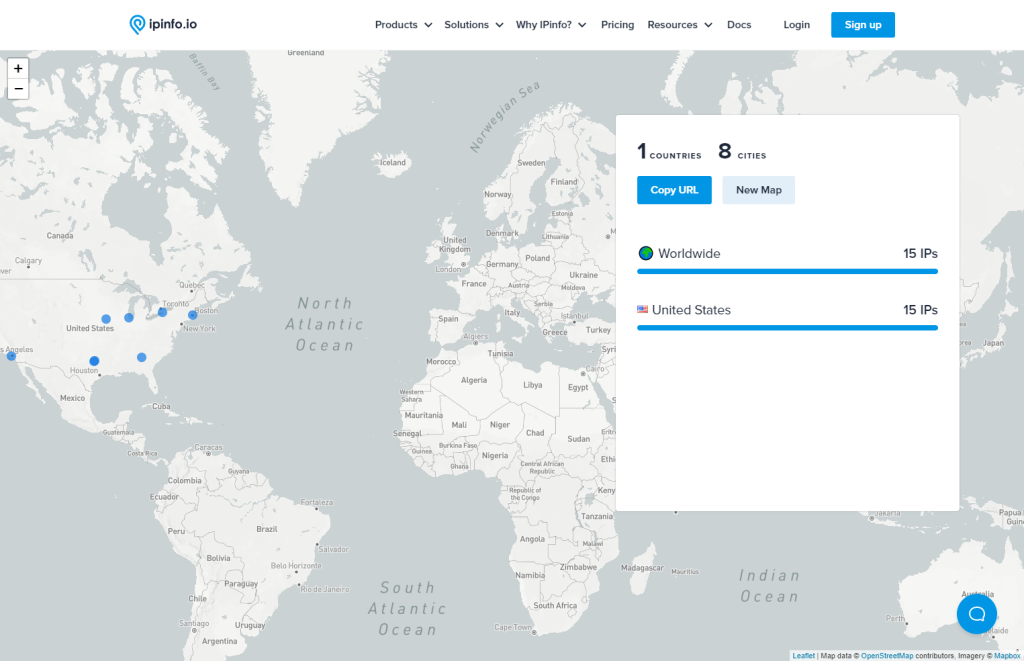
Fig 15: Map IPs w/ IPinfo.io
Fig 16: Processing Windows Event Logs (EVTX)
Fig 17: Zircolite – A standalone SIGMA-based detection tool for EVTX (Mini-GUI)
Fig 18: Processing extracted Amcache.hve → XLSX
Fig 19: Processing ShimCache → XLSX
Fig 20: Analyze CSV output w/ Timeline Explorer (TLE)
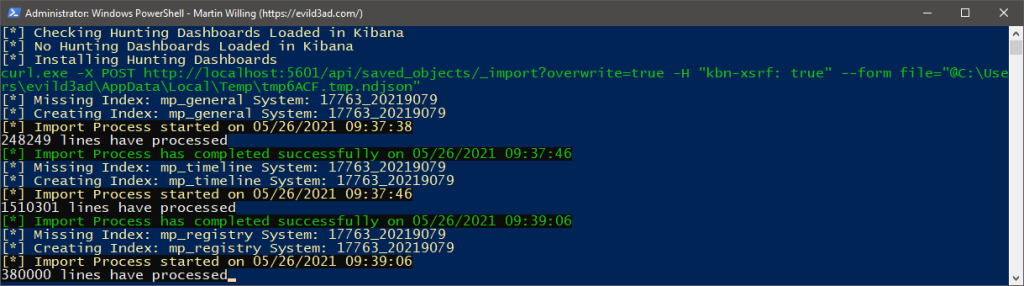
Fig 21: ELK Import
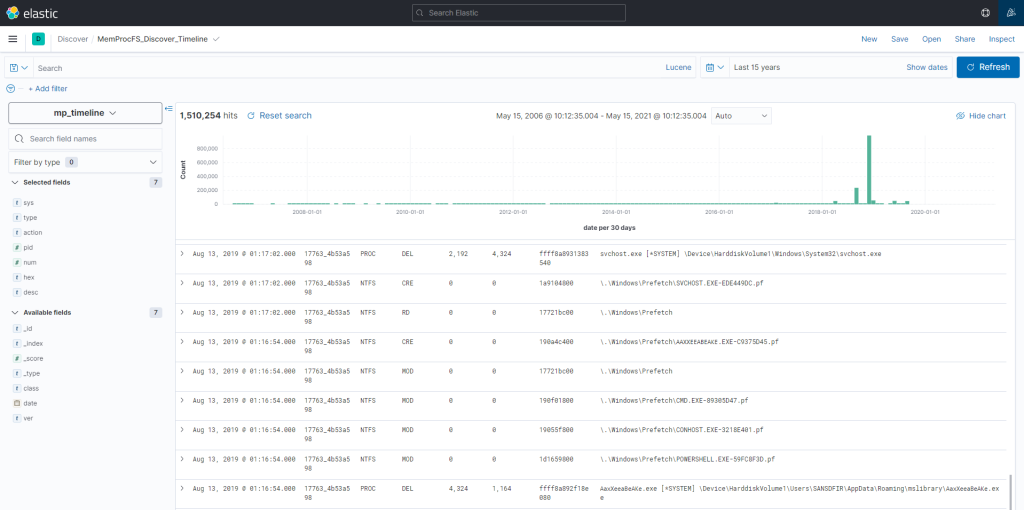
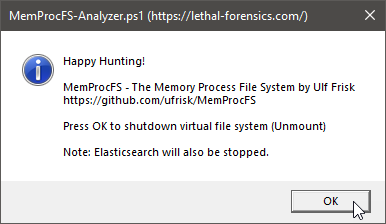
Fig 22: Happy ELK Hunting!
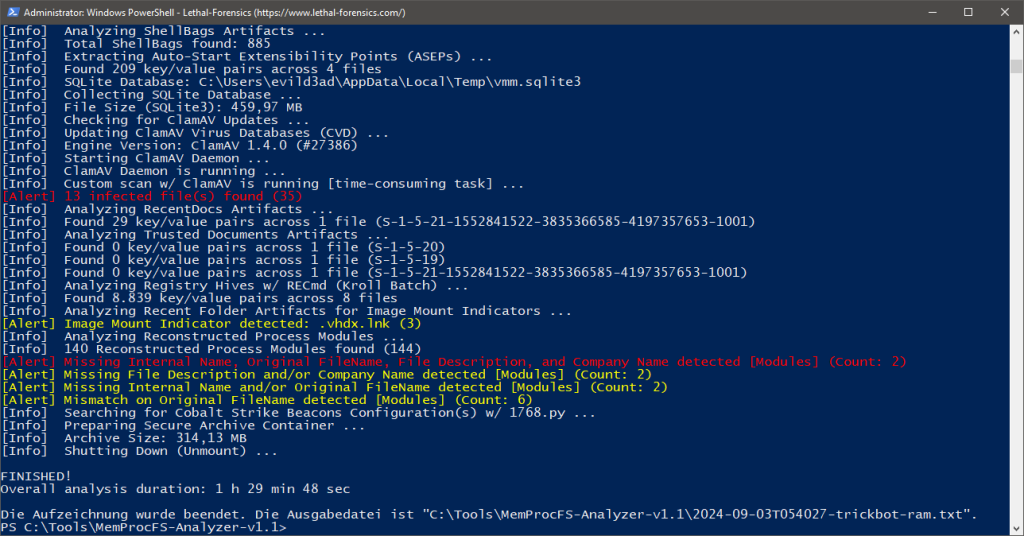
Fig 23: Multi-Threaded ClamAV Scan to help you finding evil!
Fig 24: Press OK to shutdown MemProcFS and Elastisearch/Kibana
Fig 25: Secure Archive Container (PW: MemProcFS)
Introduction MemProcFS and Memory Forensics
Check out Super Easy Memory Forensics by Hiroshi Suzuki and Hisao Nashiwa.
Prerequisites
🟢Download and install the latest Dokany Library Bundle → DokanSetup.exe
https://github.com/dokan-dev/dokany/releases/latest
🟢Download and install the latest .NET 6 Desktop Runtime (Requirement for EZTools)
https://dotnet.microsoft.com/en-us/download/dotnet/6.0
🟢Download and install the latest Windows package of ClamAV → .msi
https://www.clamav.net/downloads#otherversions
🟢First Time Set-Up of ClamAV
Launch Windows PowerShell console as Administrator.
cd “C:\Program Files\ClamAV”
copy .\conf_examples\freshclam.conf.sample .\freshclam.conf
copy .\conf_examples\clamd.conf.sample .\clamd.conf
write.exe .\freshclam.conf → Comment or remove the line that says “Example”.
write.exe .\clamd.conf → Comment or remove the line that says “Example”.
https://docs.clamav.net/manual/Usage/Configuration.html#windows
🟢Optimize ClamAV scan speed performance (30% faster)
Open “C:\Program Files\ClamAV\clamd.conf” with your text editor and search for: “Don’t scan files and directories matching regex”
ExcludePath “\\heaps\\”
ExcludePath “\\handles\\”
ExcludePath “\\memmap\\vad-v\\”
ExcludePath “\\sys\\pool\\”
🟢Create your free IPinfo account [approx. 1-2 min]
https://ipinfo.io/signup?ref=cli
Open “MemProcFS-Analyzer.ps1” with your text editor, search for “Please insert your Access Token here” and copy/paste your access token.
🟢Install the NuGet package provider for PowerShell
Check if NuGet is available in the package providers by running the following command:
Get-PackageProvider -ListAvailable
If NuGet is not installed on your system yet, you have to install it.
Install-PackageProvider -Name NuGet -Force
🟢Make sure to comment/uncomment (selectively enable or disable) the functions you want to play with (Elasticsearch and ELKImport are disabled by default). Check out the “Main” in the bottom of the script.
🟢Done!
Notes:
- Turn off your antivirus protection temporarily or better exclude your MemProcFS-Analyzer directory from scanning.
- Elasticsearch Tips
Dependencies
7-Zip 24.08 Standalone Console (2024-08-11)
https://www.7-zip.org/download.html
AmcacheParser v1.5.1.0 (.NET 6)
https://ericzimmerman.github.io/
AppCompatCacheParser v1.5.0.0 (.NET 6)
https://ericzimmerman.github.io/
ClamAV – Download → Windows → clamav-1.4.1.win.x64.msi (2024-09-04)
https://www.clamav.net/downloads
Dokany File System Library v2.2.0.1000 (2024-08-18)
https://github.com/dokan-dev/dokany/releases/latest → DokanSetup.exe
Elasticsearch 8.16.0 (2024-11-12)
https://www.elastic.co/downloads/elasticsearch
entropy v1.1 (2023-07-28)
https://github.com/merces/entropy
EvtxECmd v1.5.0.0 (.NET 6)
https://ericzimmerman.github.io/
ImportExcel v7.8.10 (2024-10-21)
https://github.com/dfinke/ImportExcel
IPinfo CLI 3.3.1 (2024-03-01)
https://github.com/ipinfo/cli
jq v1.7.1 (2023-12-13)
https://github.com/stedolan/jq
Kibana 8.16.0 (2024-11-12)
https://www.elastic.co/downloads/kibana
lnk_parser v0.2.0 (2022-08-10)
https://github.com/AbdulRhmanAlfaifi/lnk_parser
MemProcFS v5.12.6 – The Memory Process File System (2024-10-09)
https://github.com/ufrisk/MemProcFS
RECmd v2.0.0.0 (.NET 6)
https://ericzimmerman.github.io/
SBECmd v2.0.0.0 (.NET 6)
https://ericzimmerman.github.io/
xsv v0.13.0 (2018-05-12)
https://github.com/BurntSushi/xsv
YARA v4.5.2 (2024-09-10)
https://virustotal.github.io/yara/
Zircolite v2.30.1 (2024-10-13)
https://github.com/wagga40/Zircolite
Clone the repo from here: GitHub Link