Offensive Security Tool: msoffcrypto-tool
msoffcrypto-tool
msoffcrypto-tool (formerly ms-offcrypto-tool) by nolze, is a Python tool and library for decrypting encrypted MS Office files with password, intermediate key, or private key which generated its escrow key. It supports various MS Office file formats, including Word (MS-DOCX), Excel (MS-XLSX), and PowerPoint (MS-PPTX).
Installation
pip install msoffcrypto-tool
See Also: So you want to be a hacker?
Offensive Security and Ethical Hacking Course
Examples
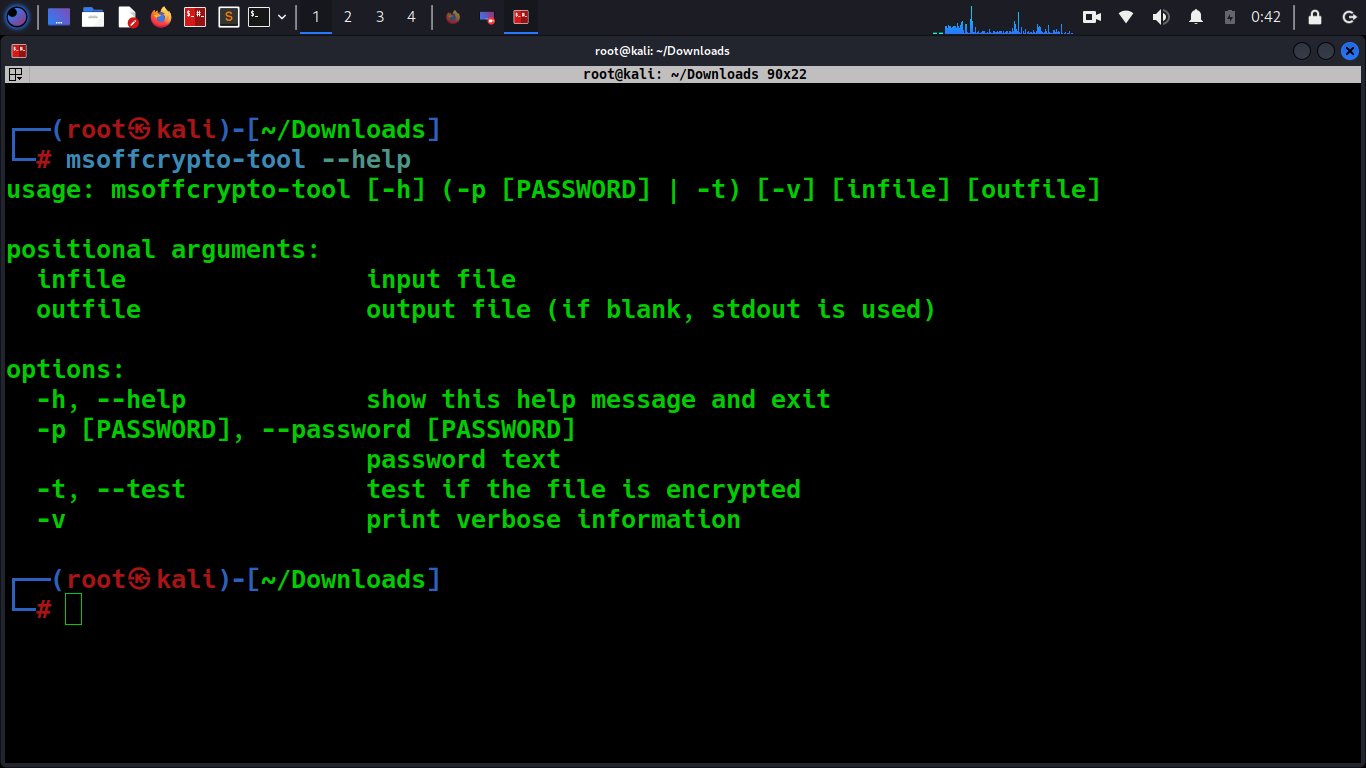
As CLI tool (with password)
msoffcrypto-tool encrypted.docx decrypted.docx -p Passw0rd
Password is prompted if you omit the password argument value:
$ msoffcrypto-tool encrypted.docx decrypted.docx -p
Password:
Test if the file is encrypted or not (exit code 0 or 1 is returned):
msoffcrypto-tool document.doc --test -v
As library
Password and more key types are supported with library functions.
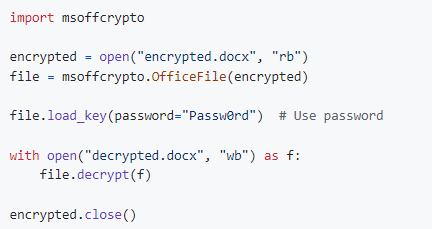
Basic usage:
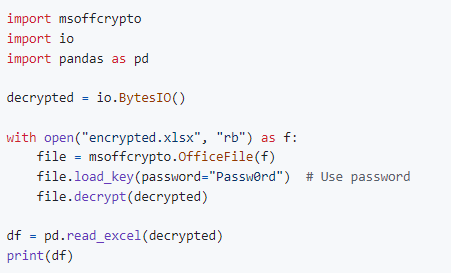
Basic usage (in-memory):
See Also: Recon Tool: Domain Analyzer
See Also: OSINT Tool: Blackbird
Advanced usage:
# Verify password before decryption (default: False)
# The ECMA-376 Agile/Standard crypto system allows one to know whether the supplied password is correct before actually decrypting the file
# Currently, the verify_password option is only meaningful for ECMA-376 Agile/Standard Encryption
file.load_key(password="Passw0rd", verify_password=True)
# Use private key
file.load_key(private_key=open("priv.pem", "rb"))
# Use intermediate key (secretKey)
file.load_key(secret_key=binascii.unhexlify("AE8C36E68B4BB9EA46E5544A5FDB6693875B2FDE1507CBC65C8BCF99E25C2562"))
# Check the HMAC of the data payload before decryption (default: False)
# Currently, the verify_integrity option is only meaningful for ECMA-376 Agile Encryption
file.decrypt(open("decrypted.docx", "wb"), verify_integrity=True)MS-OFFCRYPTO specs
- ECMA-376 (Agile Encryption/Standard Encryption)
- MS-DOCX (OOXML) (Word 2007-)
- MS-XLSX (OOXML) (Excel 2007-)
- MS-PPTX (OOXML) (PowerPoint 2007-)
- Office Binary Document RC4 CryptoAPI
- MS-DOC (Word 2002, 2003, 2004)
- MS-XLS (Excel 2002, 2003, 2007, 2010) (experimental)
- MS-PPT (PowerPoint 2002, 2003, 2004) (partial, experimental)
- Office Binary Document RC4
- MS-DOC (Word 97, 98, 2000)
- MS-XLS (Excel 97, 98, 2000) (experimental)
- ECMA-376 (Extensible Encryption)
- XOR Obfuscation
- MS-XLS (Excel 2002, 2003) (experimental)
- MS-DOC (Word 2002, 2003, 2004?)
Other
- Word 95 Encryption (Word 95 and prior)
- Excel 95 Encryption (Excel 95 and prior)
- PowerPoint 95 Encryption (PowerPoint 95 and prior)
See Also: A primer on OS Command Injection Attacks









