Offensive Security Tool: Offensive-Azure
Reading Time: 2 Minutes
Offensive-Azure
Offensive-Azure by blacklanternsecurity is a collection of offensive tools targeting Microsoft Azure written in Python to be platform agnostic. It offers various scripts that can be used against Microsoft Azure in different attack vectors ranging from token manipulation, domain enumeration getting info in regards to the tenant without requiring authentication and much more. Aimed at the red team and pentesters, to evaluate the setup of Azure in various environments.
See Also: So you want to be a hacker?
Complete Offensive Security and Ethical Hacking Course
The current list of tools can be found below with a brief description of their functionality.
⦿ Generates a code to be entered by the target user
⦿ Can be used for general token generation or during a phishing/social engineering campaign.
⦿ Takes in a refresh token in various ways and retrieves a new refresh token and an access token for the resource specified
⦿ Takes in an access token and parses the included claims information, checks for expiration, attempts to validate signature
⦿ Takes in a domain and enumerates as much information as possible about the tenant without requiring authentication
⦿ Takes in a username or list of usernames and attempts to enumerate valid accounts using one of three methods
⦿ Can also be used to perform a password spray
⦿ Takes in an access token or refresh token, outputs tenant ID and tenant Name
⦿ Creates text output file as well as BloodHound compatible aztenant file
⦿ Takes in an access token or refresh token, outputs all users in Azure AD and all available user properties in Microsoft Graph
⦿ Creates three data files, a condensed json file, a raw json file, and a BloodHound compatible azusers file
⦿ Takes in an access token or refresh token, outputs all groups in Azure AD and all available group properties in Microsoft Graph
⦿ Creates three data files, a condensed json file, a raw json file, and a BloodHound compatible azgroups file
⦿ Takes in an access token or refresh token, outputs all group memberships in Azure AD and all available group member properties in Microsoft Graph
⦿ Creates three data files, a condensed json file, a raw json file, and a BloodHound compatible azgroups file
⦿ Takes in an ARM token or refresh token, outputs all subscriptions in Azure and all available subscription properties in Azure Resource Manager
⦿ Creates three data files, a condensed json file, a raw json file, and a BloodHound compatible azgroups file
⦿ Takes in an ARM token or refresh token, outputs all resource groups in Azure and all available resource group properties in Azure Resource Manager
⦿ Creates two data files, a raw json file, and a BloodHound compatible azgroups file
⦿ Takes in an ARM token or refresh token, outputs all virtual machines in Azure and all available VM properties in Azure Resource Manager
⦿ Creates two data files, a raw json file, and a BloodHound compatible azgroups file
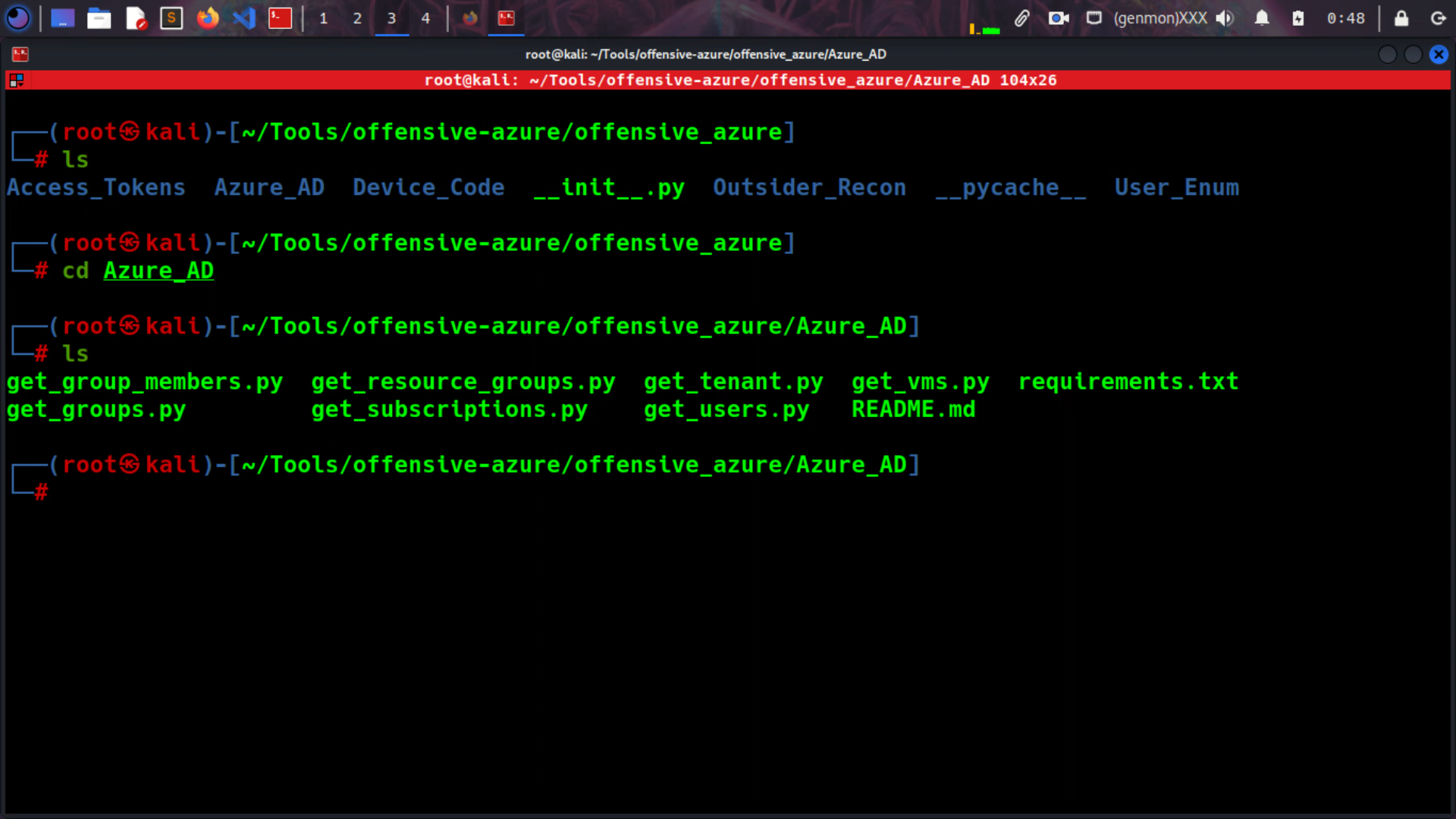
Installation
Offensive Azure can be installed in a number of ways or not at all.
You are welcome to clone the repository and execute the specific scripts you want. A requirements.txt file is included for each module to make this as easy as possible.
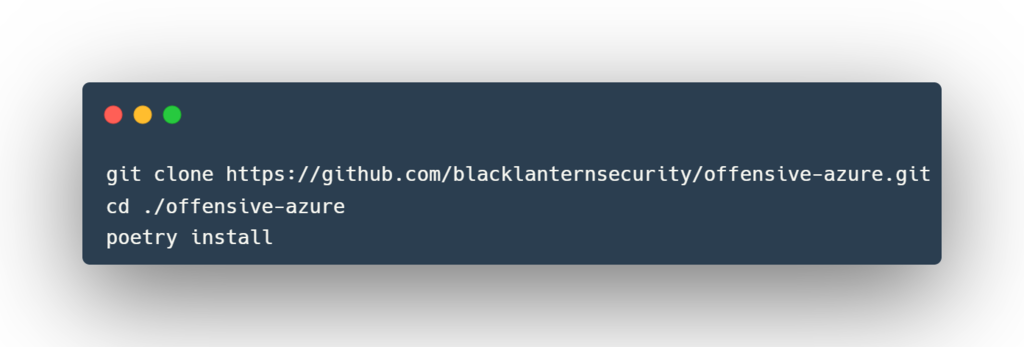
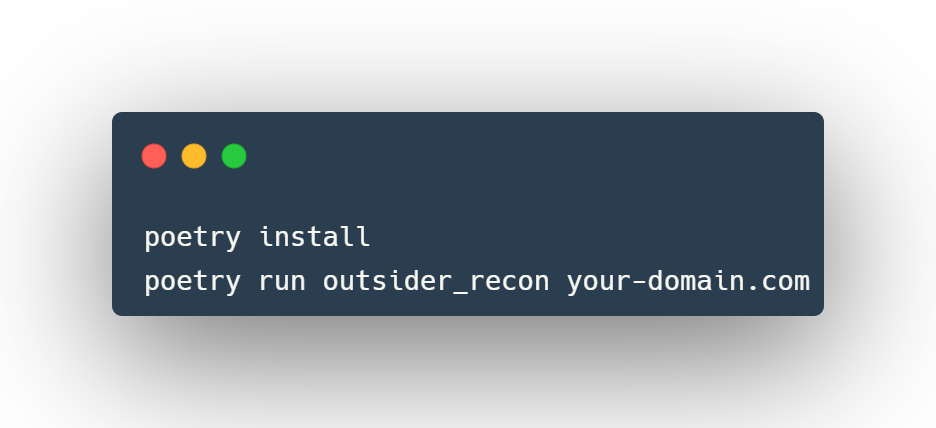
Poetry
The project is built to work with poetry. To use, follow the next few steps:
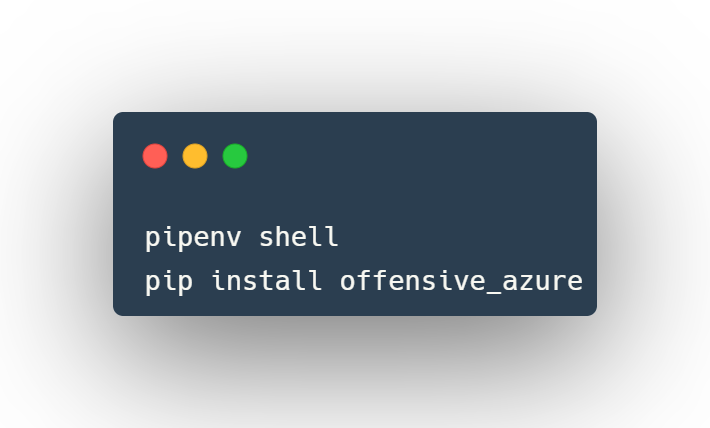
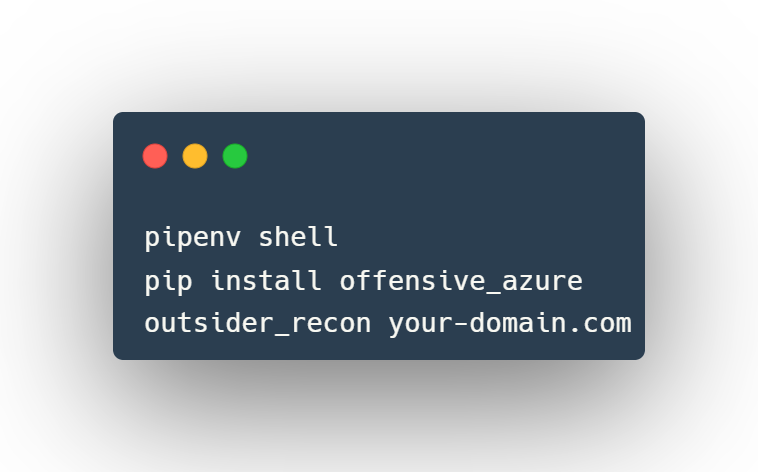
Pip
The packaged version of the repo is also kept on pypi so you can use pip to install as well. They recommend to use pipenv to keep your environment as clean as possible.
Usage
It is up to you for how you wish to use this toolkit. Each module can be ran independently, or you can install it as a package and use it in that way. Each module is exported to a script named the same as the module file. For example:
Poetry
Pip
Clone the repo from here: GitHub Link