Recon Tool: Parth
INTRODUCTION
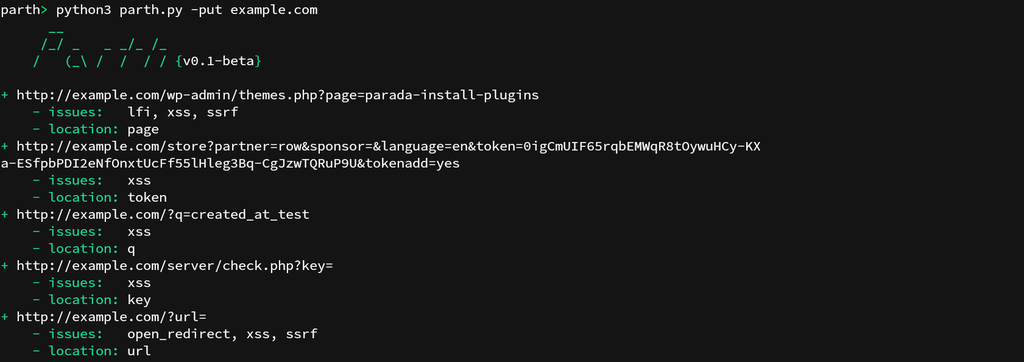
Parth by s0md3v is a Heuristic Vulnerable Parameter Scanner. Some HTTP parameter names are more commonly associated with one functionality than others. For example, the parameter “?url=“ usually contains URLs as the value and hence often falls victim to file inclusion, open redirect, and SSRF attacks. Parth can go through your burp history, a list of URLs, or its own discovered URLs to find such parameter names and the risks commonly associated with them. Parth is designed to aid web security testing by helping in the prioritization of components for testing.
See Also: So you want to be a hacker?
Complete Offensive Security and Ethical Hacking Course
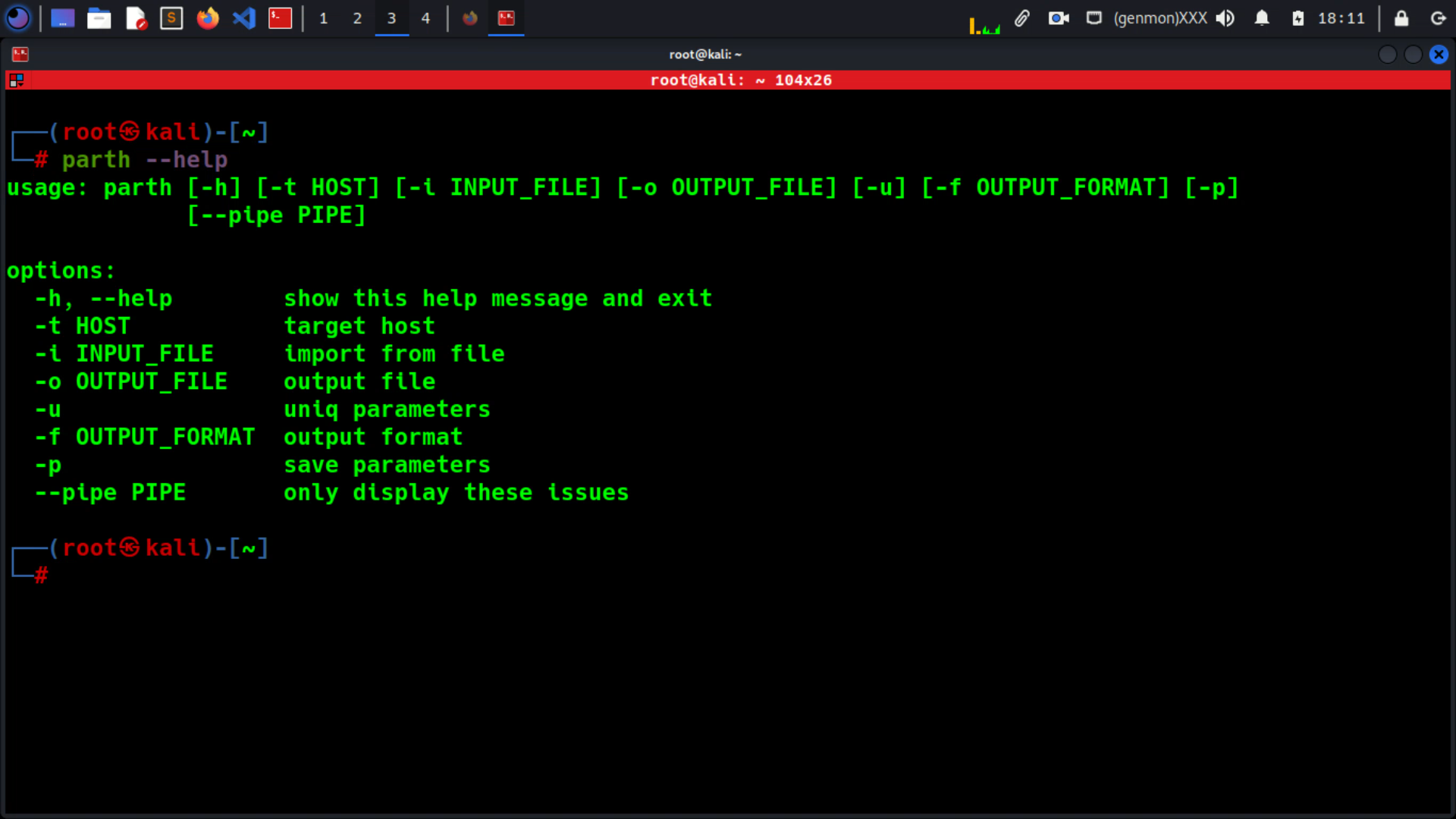
USAGE
Installation: pip3 install parth
Import targets from a file
This option works for all 3 supported import types: Burp Suite history, newline delimited text file or a HTTP request text file.
parth -i example.history
Import targets from stdin
cat urls | parth
An exclusive option –pipe is available when importing targets from stdin. It can be used to output URLs vulnerable to a specific vulnerability.
cat urls | parth --pipe xss
Supported Issues: lfi, ssrf, sqli, xss, open_redirect, rce
Trending: Offensive Security Tool: Monkey365
Trending: Recon Tool: Collector
Find URLs for a domain
This option will make use of CommonCrawl, Open Threat Exchange and Waybackmachine to find URLs of the target domain.
parth -t example.com
Ignore duplicate parameter names
Same parameter names across all URLs are ignored.
parth -ut example.com
Save parameter names
This option will write all the parameter names found in a file with name params-{target}.txt for later use.
parth -pt example.com
JSON Output
The following command will save the result as a JSON object in the specified file.
parth -t example.com -o example.json
Clone the repo from here: GitHub Link