Offensive Security Tool: SSTImap
Reading Time: 3 Minutes
SSTImap
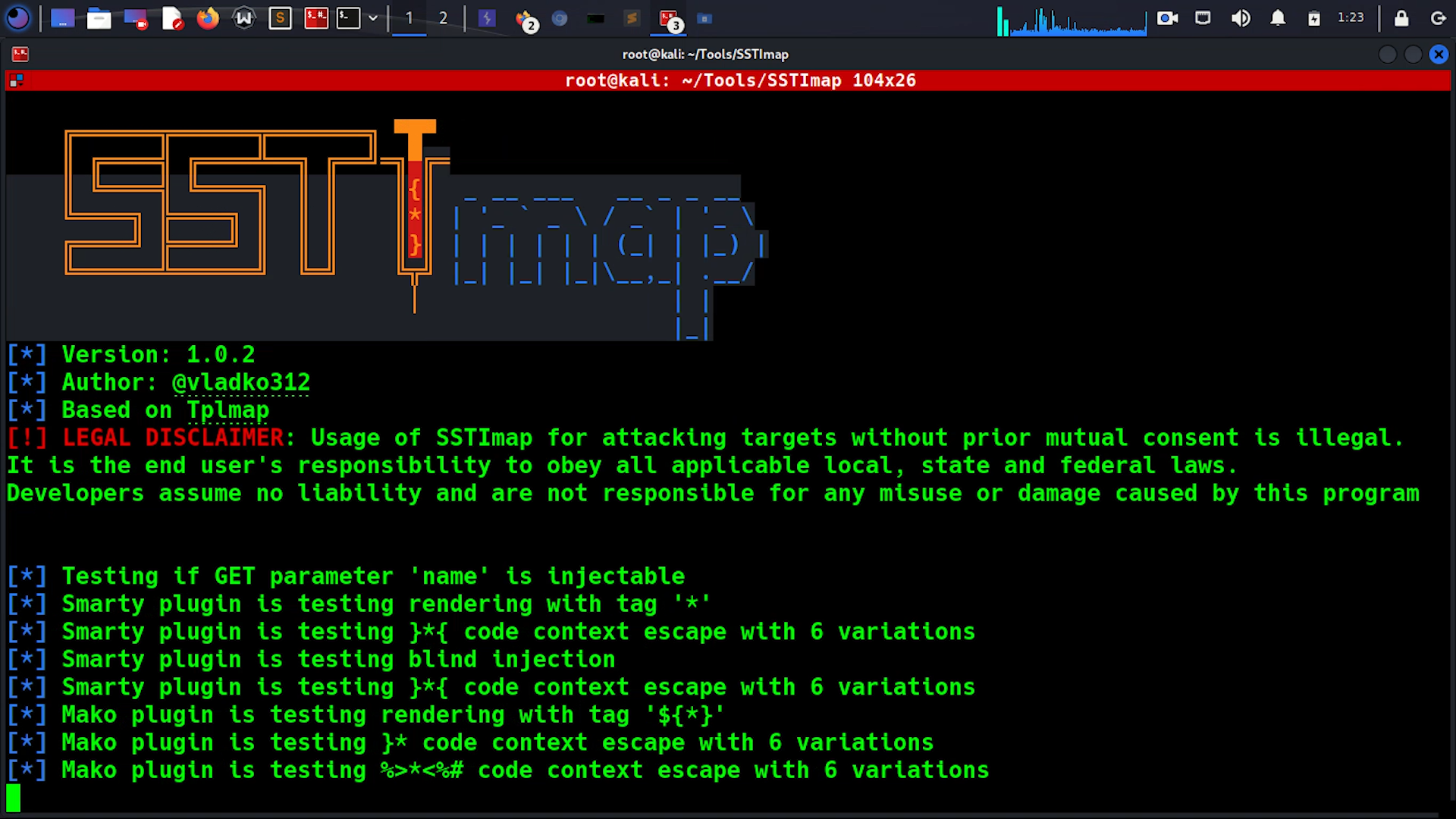
SSTImap by vladko312 is a penetration testing software that can check websites for Code Injection and Server-Side Template Injection vulnerabilities and exploit them, giving access to the operating system itself.
This tool was developed to be used as an interactive penetration testing tool for SSTI detection and exploitation, which allows more advanced exploitation.
Sandbox break-out techniques came from:
- James Kett’s Server-Side Template Injection: RCE For The Modern Web App
- Other public researches [1] [2]
- Contributions to Tplmap [3] [4].
This tool is capable of exploiting some code context escapes and blind injection scenarios. It also supports eval()-like code injections in Python, Ruby, PHP, Java and generic unsandboxed template engines.
This project is based on Tplmap.
See Also: So you want to be a hacker?
Offensive Security Courses
Differences with Tplmap
Even though this software is based on Tplmap’s code, backwards compatibility is not provided.
- Interactive mode (-i) allowing for easier exploitation and detection
- Base language eval()-like shell (-x) or single command (-X) execution
- Added new payload for Smarty without enabled {php}{/php}. Old payload is available as Smarty_unsecure.
- User-Agent can be randomly selected from a list of desktop browser agents using -A
- SSL verification can now be enabled using -V
- Short versions added to all arguments
- Some old command line arguments were changed, check -h for help
- Code is changed to use newer python features
- Burp Suite extension temporarily removed, as Jython doesn’t support Python3
Server-Side Template Injection
This is an example of a simple website written in Python using Flask framework and Jinja2 template engine. It integrates user-supplied variable name in an unsafe way, as it is concatenated to the template string before rendering.

Not only this way of using templates creates XSS vulnerability, but it also allows the attacker to inject template code, that will be executed on the server, leading to SSTI.

User-supplied input should be introduced in a safe way through rendering context:

Trending: Recon Tool: SauronEye
Trending: Offensive Security Tool: XSSRocket
Predetermined mode
SSTImap in predetermined mode is very similar to Tplmap. It is capable of detecting and exploiting SSTI vulnerabilities in multiple different templates.
After the exploitation, SSTImap can provide access to code evaluation, OS command execution and file system manipulations.
To check the URL, you can use -u argument:
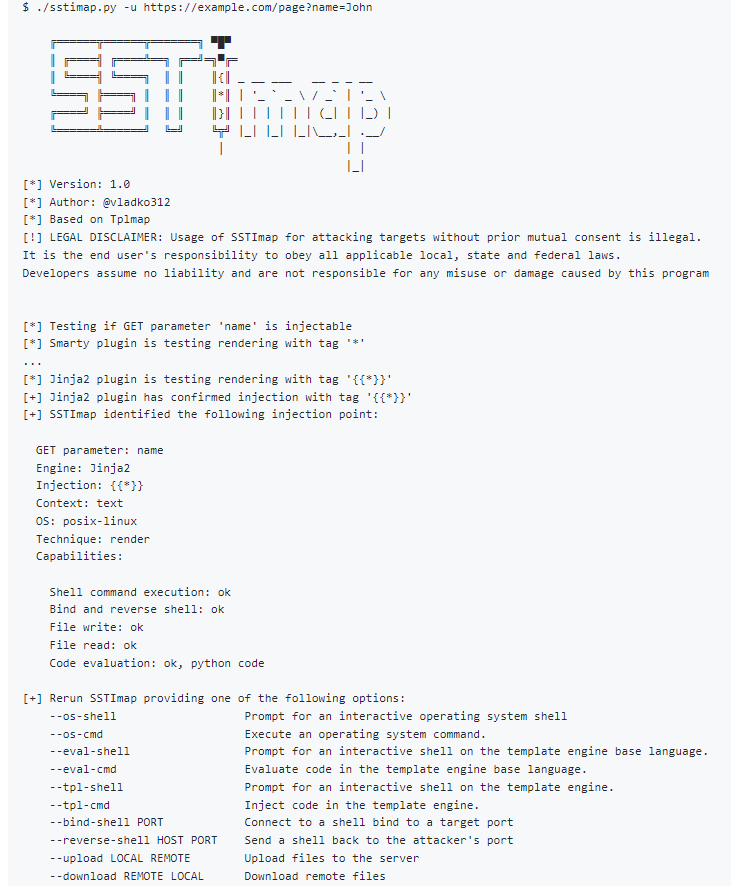
Use –os-shell option to launch a pseudo-terminal on the target.

To get a full list of options, use –help argument.
Interactive mode
In interactive mode, commands are used to interact with SSTImap. To enter interactive mode, you can use -i argument. All other arguments, except for the ones regarding exploitation payloads, will be used as initial values for settings.
Some commands are used to alter settings between test runs. To run a test, target URL must be supplied via initial -u argument or url command. After that, you can use run command to check URL for SSTI.
If SSTI was found, commands can be used to start the exploitation. You can get the same exploitation capabilities, as in the predetermined mode, but you can use Ctrl+C to abort them without stopping a program.
By the way, test results are valid until target url is changed, so you can easily switch between exploitation methods without running detection test every time.
To get a full list of interactive commands, use command help in interactive mode.
Supported template engines
SSTImap supports multiple template engines and eval()-like injections.
New payloads are welcome in PRs.
| Engine | RCE | Blind | Code evaluation | File read | File write |
|---|---|---|---|---|---|
| Mako | ✓ | ✓ | Python | ✓ | ✓ |
| Jinja2 | ✓ | ✓ | Python | ✓ | ✓ |
| Python (code eval) | ✓ | ✓ | Python | ✓ | ✓ |
| Tornado | ✓ | ✓ | Python | ✓ | ✓ |
| Nunjucks | ✓ | ✓ | JavaScript | ✓ | ✓ |
| Pug | ✓ | ✓ | JavaScript | ✓ | ✓ |
| doT | ✓ | ✓ | JavaScript | ✓ | ✓ |
| Marko | ✓ | ✓ | JavaScript | ✓ | ✓ |
| JavaScript (code eval) | ✓ | ✓ | JavaScript | ✓ | ✓ |
| Dust (<= [email protected]) | ✓ | ✓ | JavaScript | ✓ | ✓ |
| EJS | ✓ | ✓ | JavaScript | ✓ | ✓ |
| Ruby (code eval) | ✓ | ✓ | Ruby | ✓ | ✓ |
| Slim | ✓ | ✓ | Ruby | ✓ | ✓ |
| ERB | ✓ | ✓ | Ruby | ✓ | ✓ |
| Smarty (unsecured) | ✓ | ✓ | PHP | ✓ | ✓ |
| Smarty (secured) | ✓ | ✓ | PHP | ✓ | ✓ |
| PHP (code eval) | ✓ | ✓ | PHP | ✓ | ✓ |
| Twig (<=1.19) | ✓ | ✓ | PHP | ✓ | ✓ |
| Freemarker | ✓ | ✓ | Java | ✓ | ✓ |
| Velocity | ✓ | ✓ | Java | ✓ | ✓ |
| Twig (>1.19) | × | × | × | × | × |
| Dust (> [email protected]) | × | × | × | × | × |
Burp Suite Plugin
Currently, Burp Suite only works with Jython as a way to execute python2. Python3 functionality is not provided.
Clone the repo from here: GitHub Link