Offensive Security Tool: ThreatMapper

Reading Time: 2 Minutes
Description
ThreatMapper by Deepfence is a platform for runtime threat management and attack path enumeration in cloud-native environments. It actively hunts for threats in production platforms, ranking them based on their risk of exploitation. ThreatMapper reveals vulnerabilities, exposed secrets, and deviations from security best practices through a combination of agent-based inspection and agent-less monitoring.
With ThreatMapper’s ThreatGraph visualization, you can then identify the issues that present the greatest risk to the security of your applications, and prioritize these for planned protection or remediation.
- Learn more about ThreatMapper in the product documentation.
- See ThreatMapper running in the live demo sandbox.

SALE: Benefit from discounted prices on our Courses from 24/11 to 06/12.
The Bug Bounty Hunting Course
When to use ThreatMapper
ThreatMapper carries on the good ‘shift left’ security practices that you already employ in your development pipelines. It continues to monitor running applications against emerging software vulnerabilities, and monitors the host and cloud configuration against industry-expert benchmarks.
Use ThreatMapper to provide security observability for your production workloads and infrastructure, across cloud, kubernetes, serverless (Fargate) and on-prem platforms.
Planning your Deployment
ThreatMapper consists of two components:
- The ThreatMapper Management Console is a container-based application that can be deployed on a single docker host or in a Kubernetes cluster.
- ThreatMapper monitors running infrastructure using agentless Cloud Scanner tasks and agent-based Sensor Agents
See Also: Offensive Security Tool: Nucleimonst3r
The Management Console
You deploy the Management Console first, on a suitable docker host or Kubernetes cluster. For example, on Docker:
# Docker installation process for ThreatMapper Management Console
wget https://github.com/deepfence/ThreatMapper/raw/release-2.0/deployment-scripts/docker-compose.yml
docker-compose -f docker-compose.yml up --detach
Cloud Scanner tasks
ThreatMapper Cloud Scanner tasks are responsible for querying the cloud provider APIs to gather configuration and identify deviations from compliance benchmarks.
The task is deployed using a Terraform module. The ThreatMapper Management Console will present a basic configuration that may be deployed with Terraform, or you can refer to the expert configurations to fine-tune the deployment (AWS, Azure, GCP)
Sensor Agents
Install the sensor agents on your production or development platforms. The sensors report to the Management Console; they tell it what services they discover, provide telemetry and generate manifests of software dependencies.
The following production platforms are supported by ThreatMapper sensor agents:
- Kubernetes: ThreatMapper sensors are deployed as a daemonset in the Kubernetes cluster, using a helm chart.
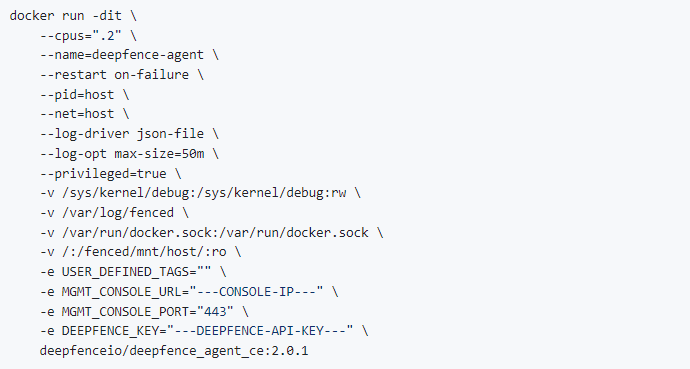
- Docker: ThreatMapper sensors are deployed as a lightweight container.
- Amazon ECS: ThreatMapper sensors are deployed as a daemon service using a task definition.
- AWS Fargate: ThreatMapper sensors are deployed as a sidecar container, using a task definition.
- Bare-Metal or Virtual Machines: ThreatMapper sensors are deployed within a lightweight Docker runtime.
For example, run the following command to start the ThreatMapper sensor on a Docker host:
On a Kubernetes platform, the sensors are installed using helm chart
Next Steps
Visit the Deepfence ThreatMapper Documentation, to learn how to get started and how to use ThreatMapper.